 Memory Grabber White Paper
Memory Grabber White Paper
- 7 pages
- May 6, 2010
The purpose of this paper is to describe the SRA Memory Grabber system, which provides memory access to a running and password protected laptop through the use of a small PC Card inserted into the PCMCIA slot of the laptop. The Memory Grabber device shown in the figure below is operating system agnostic; working on Microsoft Windows, Linux, and MacOS and is available today as a production unit for use with Express Card and Card Bus laptop systems.
…
Currently, when law enforcement agents or Special Operations personnel seize a running laptop that is password protected, they have no way of capturing the potential valuable information resident in memory. Typically, they will power down the laptop and take it back to lab to perform forensic analysis on the hard drive losing all information associated with the current state of the machine (e.g. partially constructed documents or emails, web history, or any other information that gets permanently deleted upon power down). Law enforcement agents and Special Operations personnel need a tool that provides memory access to a running laptop in the field enabling the timely capture of volatile information.
…
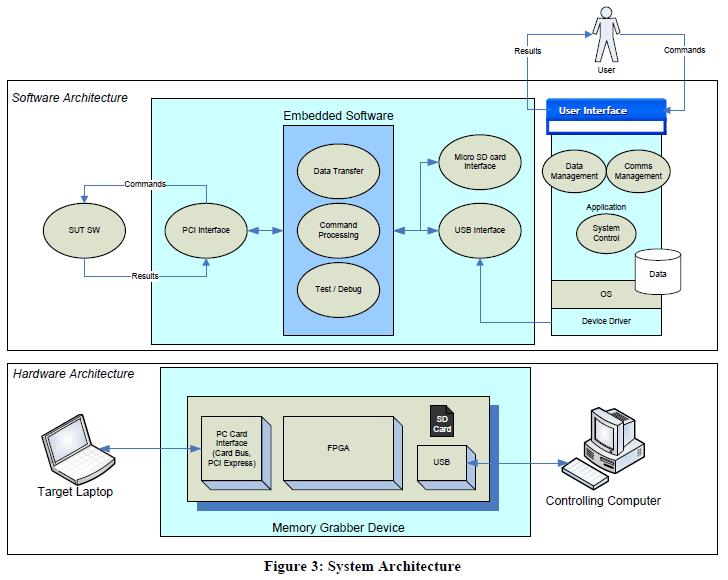
The Memory Grabber system provides direct memory access to a running laptop via a small PC card (i.e. Memory Grabber device) that can be inserted into the external PCMCIA slot, similar to commercially-available external broadband network cards. The target laptop can be screen-locked and password-protected. The Memory Grabber system can be used in either tethered or un-tethered modes (see Figure 1), and supports both Express Card and Card Bus laptop interfaces. The system can be used to acquire data from laptops running various versions of Microsoft Windows, Linux and MacOS, and supports both 32 bit and 64 bit operating systems.
…