The following bulletin from the DHS National Cybersecurity and Communications Integration Center was obtained from the website of the College of DuPage.
National Cybersecurity and Communications Integration Center
- 6 pages
- November 1, 2013
The following product is a coordinated effort between NCCIC, U.S. Secret Service and The Cyber Intelligence Network (CIN), provided to assist in prevention, detection and mitigation of a new ransomeware campaign. Ransomware is malware that restricts access to infected computers and requires victims to pay a ransom in order to regain full access. Cryptolocker is particularly interesting in that it functions by encrypting victims computer files with a combination of RSA-2048 and AES-256 encryption. Once encrypted, victims are provided a window of time in which they can pay the actors to receive the key needed to decrypt their files.
At this time, the primary means of infection appears to be phishing emails containing malicious attachments. According to a trusted third party, at least some of these emails have come from the Cutwail botnet. Cutwail is a well-known spam botnet that has previously launched campaigns distributing the Gameover Zeus Trojan among other forms of malware. This may indicate that those responsible for this campaign are using third party cyber-crime services to spread this malware. In addition, there have been reports that some victims had the malware dropped onto their machines through a preexisting backdoor existing from a previous infection with Zeus botnet malware. This may indicate the actor’s use of a pay per install third party service.
Malicious emails have been delivered with various lures including subject lines payroll or package tracking from UPS, and FedEx; as well as bank correspondence and voicemail notifications. Some identified keywords used in these emails include:
Payroll Received by Intuit
ADP RUN: Payroll Processed Alert
Payroll Manager Payroll Invoice ADP RUN
Payroll Processed Alert Annual form ACH Notification
Annual Form – Authorization to Use Privately Owned Vehicle on State Business
DNB Complaint – (Number)In addition, the malware has the ability to locate files located within shared network drives, USB drives, external hard drives, network file shares and even some cloud storage drives. This means that if the malware can infect one user who has access to all the shared file drives within an organization’s network, it’s possible all those files may become encrypted.
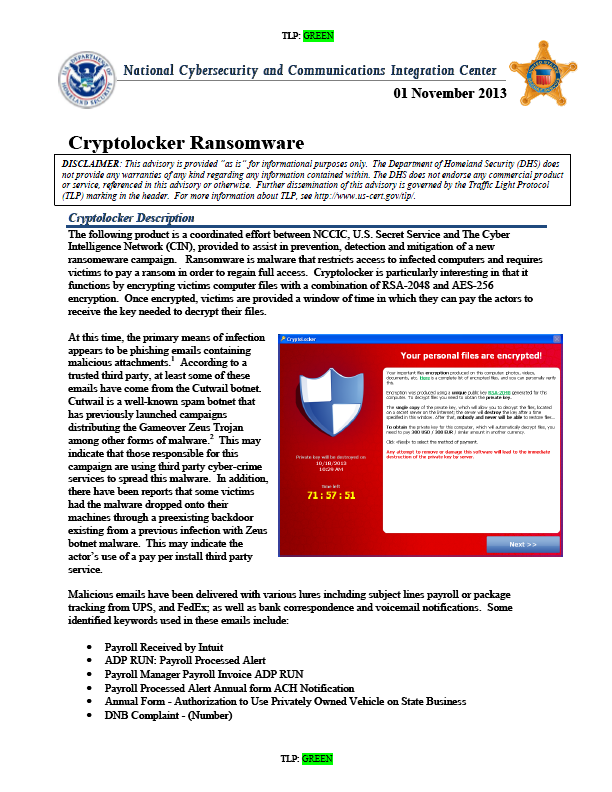
Due to the nature of asymmetric encryption, victims need access to a private key to decrypt their files. Unfortunately, this private key is stored on the actors C2 server. When the malware finishes the encryption process, a warning message appears on the victims screen indicating their files have been encrypted and to recover them, the victim needs to pay a fine of between 100 – 300 Dollars or Euros. Payment is accepted via bitcoin, GreenDot or MoneyPak. The message indicates that victims have a window of between 72 – 100 hours to pay the ransom or the private key needed to decrypt the files will be deleted from the C2 and victims will lose the ability to decrypt affected files. Each public and private key combination is different so one victim’s private key will not work to decrypt the files of another victim. It should be noted that the actors behind this campaign are not stealing victim information; they are simply holding it hostage.
Unfortunately once the malware has successfully encrypted a victims files there is no way to decrypt them without the private key. This highlights the importance of backing up files as the best method of system recovery is to remove the malware and restore files from backup. Reports indicate that users who have paid the fine have been able to get their files back. However, some of the C2 servers are being taken offline and payments sent by users have not been received, leaving the victim poorer without the decryption key. Some victims have claimed online that by posting complaints on public forums discussing Cryptolocker, they have received “customer support” from the malicious actors themselves who have assisted the victims in ensuring their payment is registered and that they receive the decryption key. As awareness of this malware continues to spread, antivirus vendors are updating their signatures to detect its presence.
…
Technical Indicators
Cryptolocker does not need special or privileged account access to perform this function. According to reports, the malware targets victims running Windows 7, Vista, and XP operating systems.
Victim files are encrypted using Asymmetric encryption. Asymmetric encryption, as opposed to symmetric encryption uses two different keys for encrypting and decrypting messages. Asymmetric encryption is a more secure form of encryption as only one party is aware of the private key, while both sides know the public key. This allows encrypted messages to be sent where only the message receiver has the key needed to decrypt the message or file.When initial infection occurs, Cryptolocker saves itself as a randomly named file within the %AppData% or %LocalAppData% and creates an autostart entry in the registry so that the malware launches when a user logs in. When the malware installs it will make a POST request to a hard-coded IP address or domain (e.g., http: / / 184.164.136.134 / home / ). This Command and Control (C2) has changed multiple times as it was flagged for abuse by security researchers. If a connection to the hardcoded C2 cannot be made, the malware seeks a live C2 server by using Domain Generation Algorithm (DGA). This algorithm allows the malware to generate 1,000 domains per day and seeks the first available connection. When the malware locates a C2 it sends an RSA-encrypted payload containing information about the malware version, the system language, an ID and Group ID. The C2 then responds with a public key made for that infected host. That key is then used to seek out a wide range of file extensions on the victim’s machine and begin the encryption process. These extensions include:
*.odt, *.ods, *.odp, *.odm, *.odc, *.odb, *.doc, *.docx, *.docm, *.wps, *.xls, *.xlsx, *.xlsm, *.xlsb, *.xlk, *.ppt, *.pptx, *.pptm, *.mdb, *.accdb, *.pst, *.dwg, *.dxf, *.dxg, *.wpd, *.rtf, *.wb2, *.mdf, *.dbf, *.psd, *.pdd, *.pdf, *.eps, *.ai, *.indd, *.cdr, *.jpg, *.jpe, img_*.jpg, *.dng, *.3fr, *.arw, *.srf, *.sr2, *.bay, *.crw, *.cr2, *.dcr, *.kdc, *.erf, *.mef, *.mrw, *.nef, *.nrw, *.orf, *.raf, *.raw, *.rwl, *.rw2, *.r3d, *.ptx, *.pef, *.srw, *.x3f, *.der, *.cer, *.crt, *.pem, *.pfx, *.p12, *.p7b, *.p7c.
The following file paths are known to have been used by this infection and its droppers:
XP
- C: \ Documents and Settings \ <User> \ Application Data \ <random name>.exe
- C: \ Documents and Settings \ <User> \ Local Application Data \ <random name>.exe
Windows Vista / 7
- C: \ Users \ <User> \ AppData \ Local \ <random name>.exe
- C: \ Users \ <User> \ AppData \ Local \ <random name>.exe
Cryptolocker samples have saved themselves as randomly named files in the %AppData% (XP) or %LocalAppData% (Vista / 7) folder and have added to the following registry key, which is used to autostart
Cryptolocker when users log into their computers:
- HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ Run
It also modifies the following registry key to include “CryptoLocker_<version_number>” for a redundant start:
- HKCU \ Software \ Microsoft \ Windows \ CurrentVersion \ RunOnce
IP Indicators:
192.210.230.39 [USA – NY]
194.28.174.119 [Ukraine]
212.71.250.4 [England]
86.124.164.25 [Romania]
87.255.51.229 [Netherlands]
93.189.44.187 [Russia]