APIS Pre-Departure Final Rule
Secure Flight Final Rule
Visa Waiver Program – Electronic System for Travel Authorization Interim Final Rule
- SF-BAP-1020 Ver 3.4
- 102 pages
- Sensitive Security Information
- May 14, 2010
EXECUTIVE SUMMARY
The Department of Homeland Security (DHS) merges the capability to anticipate, preempt, and deter threats to the homeland whenever possible through its component agencies. Under the guidance of its Screening Coordination Office, DHS directed U.S. Customs and Border Protection (CBP) and the Transportation Security Administration (TSA) to combine the Advance Passenger Information System (APIS) Pre-Departure and Secure Flight concepts and systems to provide “One DHS Solution” to the commercial aviation industry consistent with applicable authorities and statutes. This joint approach would:
• Standardize Secure Flight and APIS Pre-Departure. TSA and CBP are coordinating their airline industry needs with the intent of providing a single DHS system to the fullest extent possible;
• Reduce unnecessary programming by aircraft operators; and
• Provide consistent treatment for passengers across all aircraft operators.The Consolidated User Guide (CUG) provides technical and operational guidance to comply with the APIS Pre-Departure Final Rule and the technical and operational requirements to comply with the Secure Flight Final Rule.
Responsibility for watch list matching is planned for transition from aircraft operators to DHS in the following phases:
Phase I
International Itineraries
From the time that an aircraft operator is compliant with APIS Pre-Departure, DHS will perform watch list matching for international itineraries to and from the United States. Until the Secure Flight Final Rule is effective, aircraft operators will perform domestic watch list matching internally for wholly domestic itineraries.
Phase II
Domestic Itineraries
As specified in the Aircraft Operator Implementation Plan in the aircraft operators’ security program, DHS will assume the watch list matching responsibility for itineraries between two U.S. airports including commonwealth territories of the United States: American Samoa, Guam, Northern Mariana Islands (CNMI), U.S. Virgin Islands, Puerto Rico, Saipan (part of the Northern Mariana Islands)
Phase III
Domestic, International Itineraries, Overflights and International to International U.S. Covered Flights
DHS will transition the watch list matching function for covered flights to and from the United States from APIS Pre-Departure to Secure Flight. CBP will continue the operation of Pre Departure APIS, but will cease providing a watch list matching result for covered flights. Secure Flight will assume responsibility for watch list matching for covered flights overflying the continental United States. Additionally, Secure Flight will assume responsibility for watch list matching for covered flights between two non-U.S. locations operated by U.S. aircraft operators.
Subsequent Phases
DHS will also be assuming responsibility for watch list matching for aircraft operator direct employees.
In response to aviation industry requests to ease the compliance burden, DHS developed a single portal called the DHS Router to provide network connectivity for individual aircraft operators. The router validates message formats, filters data provided, and routes messages to CBP and TSA based on their respective missions.
To describe the data elements in APIS Pre-Departure and Secure Flight, DHS will use the term “passenger data.” Passenger data represents the information used to identify the passenger or non-traveler.
To clarify between data for Secure Flight and APIS Pre-Departure, DHS will refer to passenger data associated with Secure Flight as Secure Flight Passenger Data (SFPD). Passenger data for international travel associated with APIS Pre-Departure requirements will be referred to as APIS data.
DHS uses the term “Passenger Data Message” to refer to the message that aircraft operators will use to submit passenger data to DHS. The two formats accepted will be UN/EDIFACT (PAXLIST) or XML. Section 4, the Technical Requirements Guide, contains details regarding Passenger Data Messages.
…
2.1 APIS Pre-Departure Final Rule
The Advance Passenger Information System (APIS) is a program within CBP that screens passengers and crewmembers traveling on international flights. Developed in 1988, APIS collects biographical data from international air passengers traveling into or departing from the United States. Aircraft operators submit passenger data at pre-determined times, allowing the data to be checked against law enforcement databases.
The Intelligence Reform and Terrorism Prevention Act of 2004 (IRTPA) (Public Law 108-458) was enacted on December 17, 2004. Sections 4012 and 4071 of the IRTPA require DHS to issue regulations and procedures to allow for pre-departure watch list matching of passengers onboard aircrafts arriving in and departing from the United States, and of passengers and crew onboard vessels arriving in and departing from the United States.
The processing of passenger manifests in APIS will continue to support the existing UN/EDIFACT PAXLST passenger manifest format, as currently submitted by aircraft operators. The options discussed in this document do not supersede any of the data requirements or aircraft operator responsibilities specified within the APIS Final Rule (see Federal Register, Volume 70, No. 66 [70FR17820]).
Aircraft operators that fail to transmit APIS data in accordance with the APIS Pre-Departure Final Rule may be subject to civil and monetary penalties. Aircraft operators must validate APIS data based on what is found in the Machine Readable Zone of the provided travel document. Aircraft operators unable to utilize the technology provided with a document swipe are required to validate the data found in the Machine Readable Zone, full name, date of birth, document type, document number, document country of issuance, document expiration date, and gender. Validation may equal a visual comparison of the individual’s travel document with the data submitted to DHS.
…
2.2 Secure Flight Final Rule
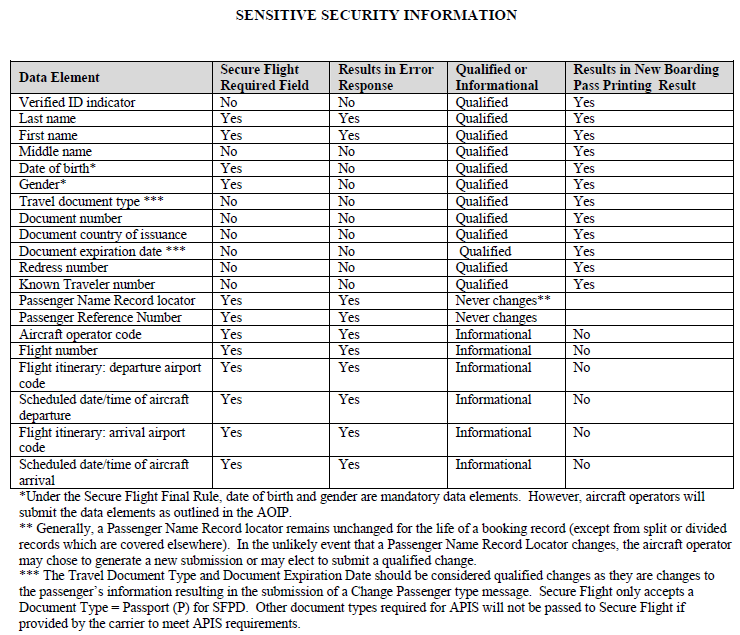
Secure Flight TSA is assuming the watch list matching function from aircraft operators (currently carrying out this function under TSA security directives and emergency amendments) and CBP (for covered flights to and from the United States). To assume this function, TSA requires aircraft operators to collect information from passengers, transmit that information to TSA for watch list matching purposes, and process passengers in accordance with TSA instructions regarding boarding pass printing results.
TSA requires aircraft operators to request and collect passengers’ full name, gender, date of birth, and Redress Number (if available; see Section 5.4 for details) or Known Traveler Number (if available). Aircraft operators must then transmit to TSA the Secure Flight Passenger Data (SFPD) record containing the information provided for each passenger, as well as passport information (if available), and certain non-personally identifiable information used to manage messages, including itinerary information. Itinerary information is required to support appropriate levels of regional security.
For non-travelers (who are not otherwise authorized, e.g., on-duty employees) seeking authorization to enter an airport sterile area in the U.S. (such as to escort a minor or disabled passenger), TSA is requiring aircraft operators to request the same data from these individuals as from passengers. Under the Final Rule, aircraft operators will transmit to TSA that information as well as certain non-personally identifiable information used to manage messages, including the airport code for the sterile area to which the non-traveler seeks access.
Under the Secure Flight Final Rule, TSA will match the information provided by aircraft operators against the watch list. Based on the boarding pass printing results, TSA will instruct an aircraft operator to process the individual in the normal manner, to identify the individual for enhanced screening at a security checkpoint, or to deny the individual transport or authorization to enter the airport sterile area. To ensure the integrity of the boarding pass printing results and to prevent the use of fraudulent passes, TSA will work with the airline industry to design a solution using a bar code or optical character code on boarding passes. This concept will be developed at a future date.
This Final Rule requires passengers and non-travelers to provide full name, date of birth, and gender.
…
2.3 ESTA Interim Final Rule
Section 711 of the 9/11 Commission Act of 2007 requires that the Secretary of Department of Homeland Security (DHS), in consultation with the Secretary of the Department of State (DoS), develop and implement a fully automated ESTA to collect information from travelers seeking to visit the United States under the Visa Waiver Program (VWP) to determine whether the individual presents a security risk and is eligible to travel to the United States. An Interim Final Rule was published to satisfy this mandate on June 9, 2008.
ESTA is an internet enabled and accessible application that will allow individuals who wish to travel under the VWP to submit an application from anywhere in the world to obtain authorization to travel to the United States under the VWP. Approved travel authorization applications submitted via ESTA are granted for a period of two years, unless passport expiration dates limit validity, and are considered acceptable for multiple uses. Biographic information supplied by applicants is screened against law enforcement databases to identify those who may be ineligible for travel under the terms of the VWP as identified in Section 217 of the Immigration and Nationality Act or pose an elevated law enforcement risk.
…