This document is part of a collection leaked by the anonymous hacker collective known as LulzSec.
FBI Phoenix Division Cyber Crime Report
- 10 pages
- Law Enforcement Sensitive
- April 29, 2011
(U//LES) Botnet Owners Share Honeypot Internet Protocol Addresses in Attempt to Avoid Law Enforcement and Security Vendor Scrutiny
(U//LES) Between 23 February, 2011 and 15 March, 2011, Botnet owners posting on the website ryan1918.com shared internet protocol (IP) addresses they believed were associated with honeypots used by law enforcement and anti-virus, anti-malware, and security research vendors.
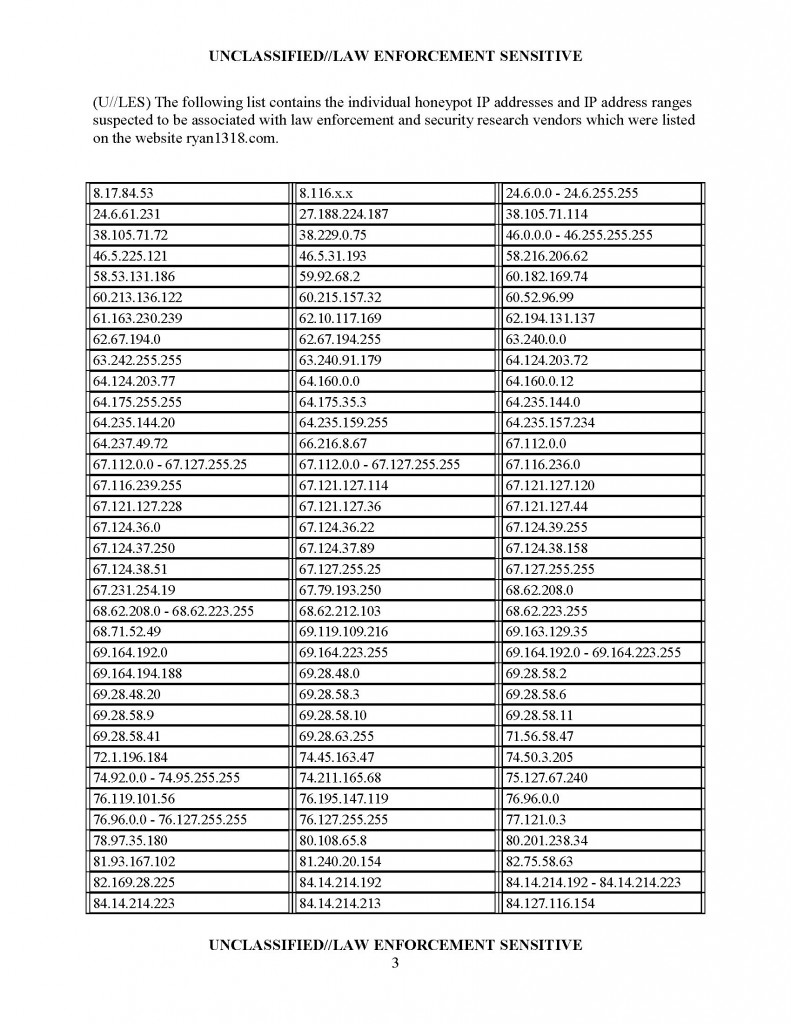
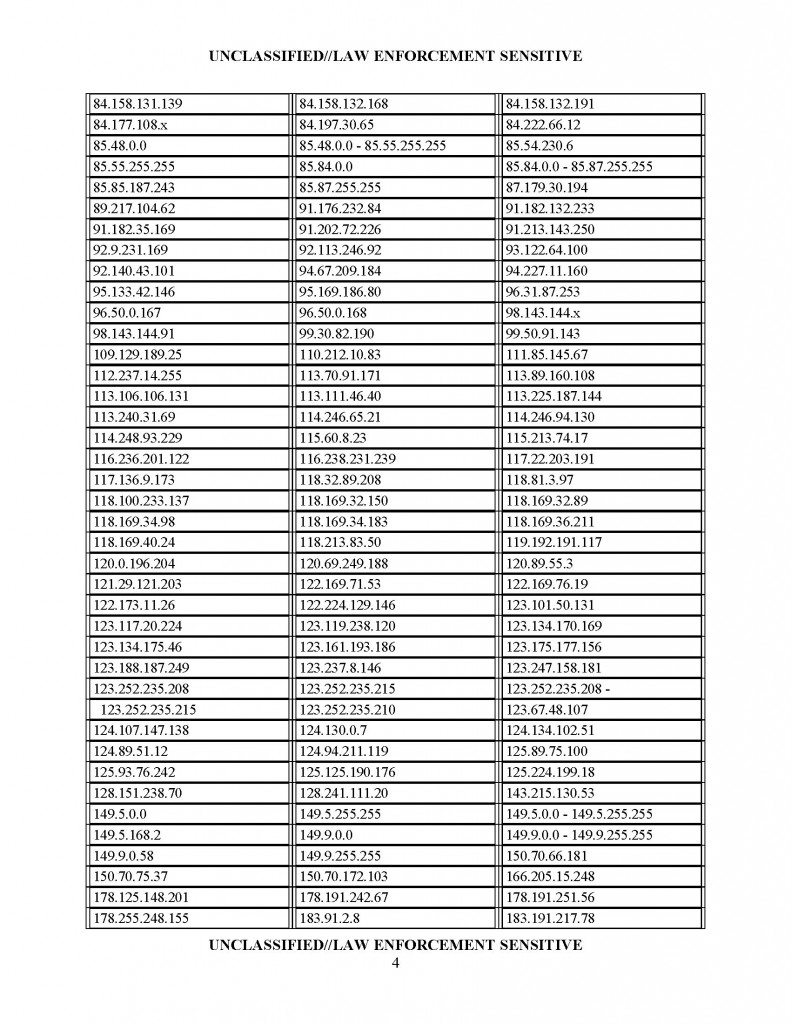
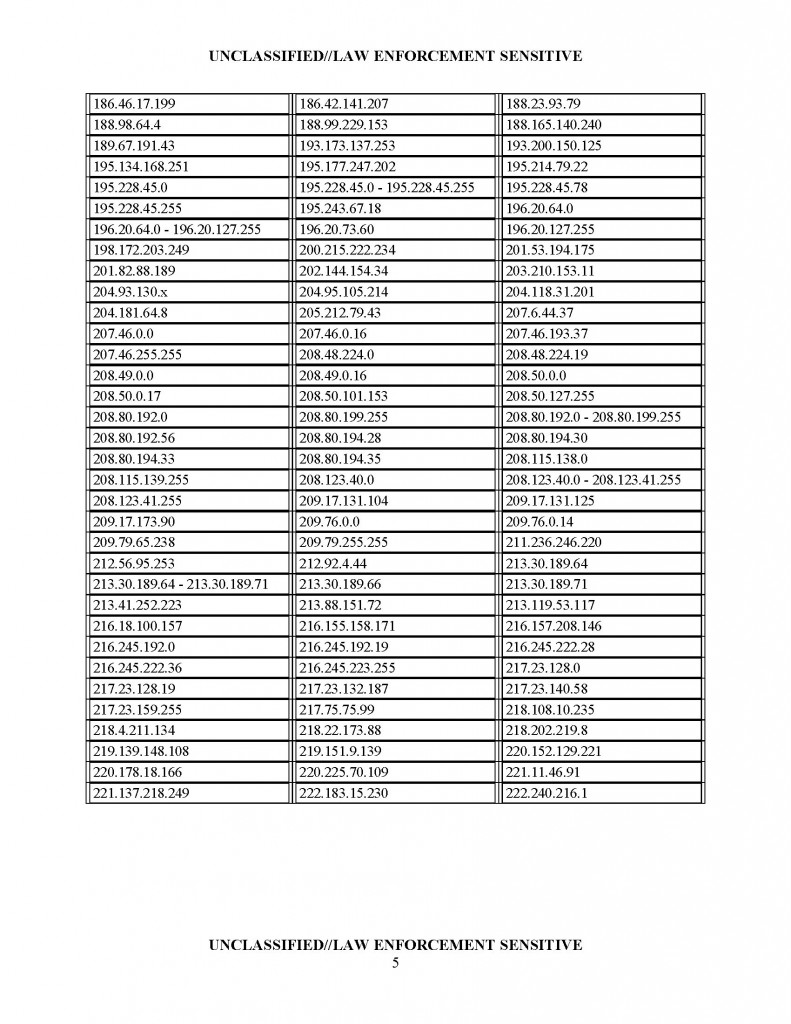
(U//LES) The Botnet owners warned the data collected by honeypots could be used by law enforcement agencies for criminal indictments. Botnet owners were further advised to be suspicious of blind “GET” requests and to use firewall rules in order to drop requests originating from the IP addresses and IP address ranges listed below.
(U//LES) The ryan1918.com website was identified in previous law enforcement reporting as the location of a collaboration forum for hackers and owners of botnets. The website allows hackers to claim credit for defacements, post hacking tools, and share hacking success stories.
…