 California Emergency Management Agency
California Emergency Management Agency
- 10 pages
- January 2010
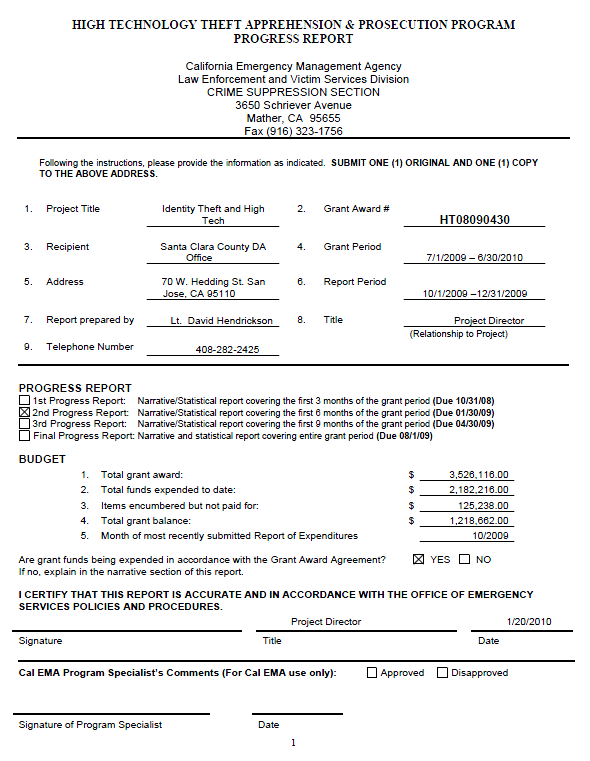
• Discuss the project’s progress to date.
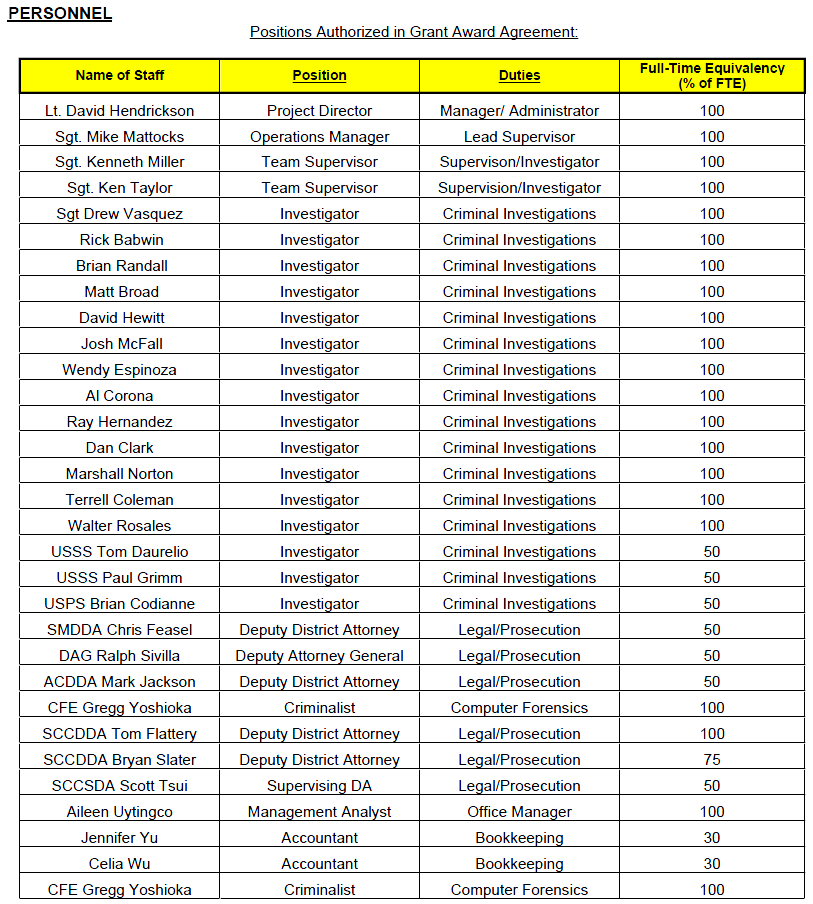
I was assigned the responsibility to organize and complete the annual report (2009) to the governor and legislature, which was accomplished on-time in December of 2009. My appreciation for their assistance goes to my staff, Administrative Analyst Aileen Uytingco and Criminalist Greg Yoshioka, as well as a special thanks to CDAA member (California District Attorney’s Association) Santa Clara County Deputy District Attorney Bud Frank and San Diego Deputy District Attorney and Project Director of the CATCH task force Brendan McHugh. Particular kudos for Brendan’s ‘Executive Summary’ and analyses of all the statistical reporting from the five task forces.
We have experienced a vacancy in REACT beginning at the start of the second quarter and may further suffer another vacancy this quarter, both from the Santa Clara County District Attorney’s Office in the Bureau of Investigation. The open positions in BOI are held in a high priority; however, it is planned that the DA’s office will backfill one of the positions after the new hires are brought into the Bureau.
In spite of all that is occurring around the REACT office and the grant in general, the task force still maintains a high degree of involvement and statistical improvement. We have had a great run of supporting media releases of cases the task force has completed that have instilled an immense level of pride in our organization and speaks to the great motivation the men and women in this organization have towards getting the job done.
Please complete the statistical report table for Objectives #1, #2, and #3. Use additional pages to provide any additional narrative to report your accomplishments as projected in your application.
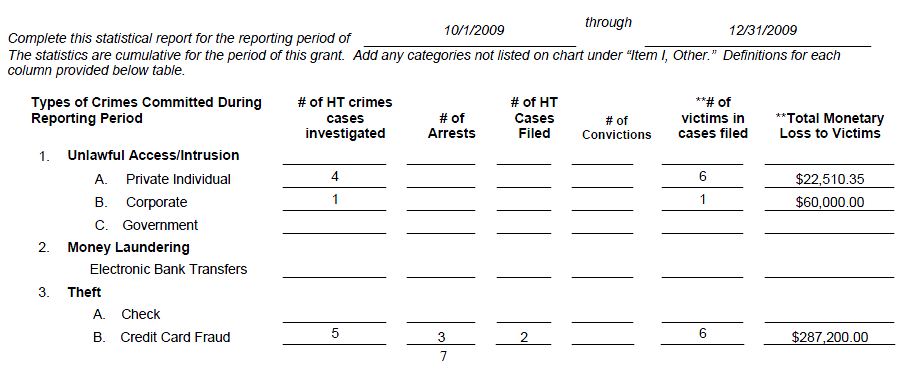
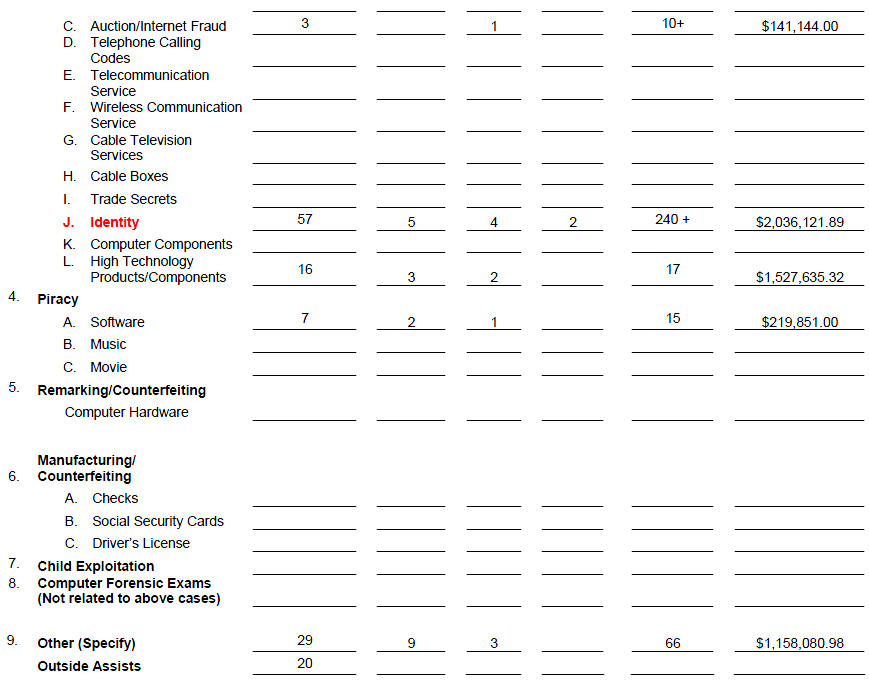
Objective #1: To investigate, apprehend, and prosecute criminal organizations, networks, and groups of individual engaged in the following activities: (The project should list the applicable high technology crimes as defined by California Penal Code § 13848 in which the task force focus is engaged.)
Objective #2: To apprehend and prosecute individuals and groups engaged in the unlawful access, destruction, or unauthorized entry into and use of private, corporate, or government computers and networks, including wireless and wireline communication networks and law enforcement dispatch systems, and the theft, interception, manipulation, destruction, and unauthorized disclosure of data stored within those computers.
Objective #3: To apprehend and prosecute individuals as groups engaged in the theft of trade secrets.
…
…
a) Significant Cases (Q2 FY09/10 (10/01/09-12/31/09)
High Tech
09-2001
An unknown person utilized the Roblox website forum located in Redwood City to make an ominous threat against an unknown school. REACT was requested to assist with the investigation.
An emergency request for records was sent and subscriber information was received. The message was traced to a 15-year-old boy in Rocky Mount, NC. Rocky Mount PD was contacted and provided with the information obtained to date. A search warrant of his residence by Rocky Mount police turned up drawings depicting explosions, but no destructive devices.
He was detained for making a false report of a destructive device and was released to the custody of his mother pending a juvenile hearing.09-2015
A Bay Area software company hired the Suspect to work on a program used by many of the company’s clients. The Suspect and the company’s president had a disagreement which resulted in the firing of the Suspect. In retaliation, the Suspect allegedly inserted a crash logic program in the software that caused the program to be down for a period of several days which ended up costing the company a loss of over $60,000.00. This investigation is on-going.09-2018
The suspect is a former employee of a large networking company headquartered in the Bay Area. He was responsible for inventory control at one of the buildings located in San Jose, CA. Investigators from the company suspect that the former employee was stealing serialized internal assets and then selling them to a local Reseller. Investigators conducted internal audits of serial number checking by a user of the Reseller. Several of those serial numbers were traced to internal owned assets that were under the control of the Suspect. Initial loss estimate is over $1,000,000.00. This investigation is on-going.
ID Theft09-1999
This case involves a possible large scale skimming operation where the points of compromise are stores from a national fabric store chain. Multiple victims have had their credit card account information compromised and then used at ATM machines all over the Bay Area.In September of 2009, FICO noticed an increase in unauthorized ATM withdrawals. After contacting banks and terminal processing companies, they determined that the common point of compromise were several fabrics stores throughout the United States. Included are victims that used the store in San Jose, CA. To date, 24 stores (locations in CA, OR, WA, UT, CO, WI, IL, TX, MO, KS, & VI) from this chain have had customers report compromised cards and unauthorized ATM withdrawals. At least 700 cards have been reported and are expected.
These actions seem to be in violation of 18 USC 1029 (access device fraud) and 18 USC 371 (conspiracy). Initial loss estimate is $1,000,000.00. This investigation is on-going.09-2028
A Target Store Employee (Suspect 1) is suspected of swiping stolen credit card numbers and loading gift cards in $500.00 increments for Suspect 2. Suspect 1 is using stolen credit card numbers from Germany to obtain these cards. Suspect 2 is selling the items that are being purchased with the fraudulently loaded gift cards on Craigslist. Initial loss estimate is $20,000.00. This investigation is on-going.09-2031
This case is the result of another REACT Case wherein victim’s information was stolen by Suspect 1 and later utilized by Suspect 2. Suspect 2 attempted to utilize the Victim’s information to obtain and cash a cashier’s check. He subsequently left his counterfeit driver’s license behind and was subsequently identified from the photo on the counterfeit driver’s license. Initial loss estimate is $4,500.00. This investigation is on-going.09-2046
The victim in this case was contacted by Ameritrade regarding someone attempting to transfer money from one of the victim’s TD Ameritrade accounts to a Wells Fargo account in the name of a third party. The Ameritrade employee stated the transfer was for over $16,000.00 and the caller knew the Victim’s SSN. The transfer was not completed because the caller could not answer the security question correctly. This investigation is on-going.09-2047
A San Jose Police Department officer made a traffic stop and contacted four occupants. He observed a laptop computer with a magnetic card reader attached on the R/F passenger floor. One passenger lied about his identity and was later arrested. The driver and remaining passengers were arrested for unlawful possession of a skimming device. Search of the driver’s purse yielded an apron from a local restaurant (Union City) and a mini skimming device. Many gift cards were also found. This investigation is on-going.…