Functional Concept for Cyberspace Operations
- 76 pages
- Distribution authorized to United States Government agencies and their contractors; Administrative or Operational Use.
- Jun 14, 2010
This functional concept details capabilities and effects necessary to perform operational cyberspace functions desired by the warfighter, from the present through 2030. This concept broadly describes how AFSPC intends to conduct cyberspace operations in support of both joint and AF operations of all types, and provides a foundation for developing more detailed concept documents. Moreover, AFSPC will use this concept, along with emerging joint guidance, to organize, train, and equip forces to conduct cyberspace operations. Finally, this concept provides the operational perspective to underpin the many activities necessary to realize the AF institutional vision for a mature set of cyberspace capabilities:
• Position the AF with enhanced and differentiated capabilities complementing those of other Services
• Assure the mission by securing the AF portion of the Department of Defense (DoD) Global Information Grid (GIG)
• Fuse cyberspace and intelligence, surveillance, reconnaissance (ISR) functions to create seamless operations
• Create unique capabilities through innovation and integration
• Build the next-generation network/cyberspace infrastructure
• Refine operations to create synergies and seamless capabilities
• Field and further develop operationally responsive capabilities
• Achieve cyberspace integration and acculturation…
3.2 Military Challenges
3.2.1 Threats to Cyberspace Operations
Cyberspace exploitation and attack have grown more sophisticated and more serious. Our information technology infrastructure—including the Internet, telecommunications networks, wireless communications, computer systems, and embedded processors and controllers—is targeted for exploitation, and potentially for disruption or destruction, by a growing array of state and non-state adversaries. Adversaries can be structured or unstructured, well-organized and well-funded with long-term objectives; or smaller, less organized groups with limited support and motives. Structured threats include activities by state-sponsored, criminal-sponsored, or hostile or radically-oriented groups with generally long-term objectives. Unstructured threats are generally those threats that originate from individuals or small groups with a limited support structure and limited motives. In either case, adversaries may capitalize on low-entry costs, widely available civilian and commercial resources, and minimal technological investment to potentially inflict serious harm. The expanded availability of commercial off-the-shelf (COTS) technology provides adversaries with increasingly flexible and affordable technology to adapt for hostile purposes. These low barriers to entry make cyberspace targets and the cyberspace domain attractive to adversaries. A related threat is the ―insider‖ who has some level of authorized access to information and information infrastructure within an organization.
The risk of a cyberspace loss or failure must be considered when planning and executing AF operations, to include mitigation actions and/or alternatives.
3.2.2 Mission Essential Functions (MEFs)
The vast number of cyber-related assets to which numerous ongoing missions depend makes it difficult to know the impact when one of those assets is rendered inoperable (intentionally or unintentionally). MEFs must be accomplished to achieve mission objectives. This entails prioritizing mission essential activities, mapping mission dependence on cyberspace systems/ assets, identifying vulnerabilities, mitigating risk of known vulnerabilities, identifying threats and adversary intent, and neutralizing the adversaries’ ability to attack/exploit friendly force vulnerabilities.
MEFs are the specified or implied tasks required to be performed by, or derived from, statute, executive order, or other appropriate guidance, and those organizational activities that must be performed under all circumstances to achieve DoD component missions. Failure to perform or sustain these functions would significantly affect the DoD’s ability to provide vital services or exercise authority, direction, and control.3.2.3 Compressed Decision Cycle of Cyberspace Operations
The fact that operations can take place nearly instantaneously requires the formulation of predetermined or automated responses to potential cyberspace attacks. The compressed decision cycle follows rules (predetermined responses) for actions that enable counterattacks against time-sensitive and fleeting targets, as allowed. This compressed decision cycle places a premium on battlespace awareness (BA). A key element of BA, particularly with regard to cyberspace operations, is intelligence preparation of the operational environment (IPOE). IPOE provides a foundational and predictive analytic understanding of the battlespace, its environment, adversary capabilities, and intent. However, to truly be effective in aiding decision making, BA must also rely on the other pillars of predictive battlespace awareness or PBA (target development, ISR strategy & planning, ISR execution, and assessment), as well as cyberspace indications and warning (I&W) and threat attribution and characterization. Through constant integration of these cyber ISR processes, friendly forces can rapidly identify potential adversary threats/courses of action (COAs) and develop plans to counter or exploit those COAs.
3.2.4 Anonymity and the Inherent Attribution
The nature of cyberspace, government policies, and international laws/treaties make it very difficult to determine the origin of cyberspace attacks and network intrusions. The ability to hide the true (originating) source of an attack makes it difficult to identify the attacker. Furthermore, the design of the Internet lends itself to anonymity. Anonymity results from:
• The large number of cyberspace users/actors
• The massive volume of information flowing through the networks
• Features that allow users to cloak their identity and activitiesThere is little the US can do about anonymity; however, the same features utilized by terrorists, hackers, and criminals (anonymity and the ability to hide) can also strengthen US surveillance and law enforcement efforts.
Attribution is a significant challenge because of the dynamic and pervasive nature of cyberspace, where flexibilities are often achieved by embedded, distributed dependencies that change frequently, and can be difficult to identify.
3.2.5 Legal Considerations
DoD must conduct cyberspace operations within applicable US laws and international agreements, and in accordance with relevant Government and DoD policies. The legal framework applicable to cyberspace operations depends on the nature of the activities to be conducted, such as offensive or defensive military operations, defense support to civil authorities, service provider actions, law enforcement and counterintelligence activities, intelligence operations, and defense of the homeland. The actions of cyber warfare6 and exploitation may have different legal and approval requirements/authorities. Before conducting cyberspace operations, commanders, planners, and operators must understand the relevant legal framework in order to comply with laws and policies. As in all other military operations, US Armed Forces conducting cyberspace operations must comply with the law of armed conflict (LOAC).
Cyberspace forces may at one moment be operating under Title 10, US Code, Armed Forces, at another moment under Title 50, US Code, War and National Defense, and even in some instances under Title 18, US Code, Crimes and Criminal Procedure. In addition, some cyberspace forces may operate under Title 32, US Code, National Guard. The rules for operating under different Titles of US Code are very different, and the authority to transition from one to another may be held at a very high level (even that of the President of the United States).
3.3 Assumptions
The following assumptions guide the formulation of this functional concept:
• Resources are in place and the AF is committed to increasing and improving cyberspace mission capabilities. Ineffective cyberspace mission capabilities will significantly reduce the AF’s ability to understand, shape, and command the cyberspace domain for the joint warfighter
• Both traditional and irregular forms of warfare will require cyberspace defensive, exploitative, and offensive elements
• Timely and responsive requirements, acquisition, certification, integration, and testing processes are in place to field cyberspace capabilities
• Adversaries will continue to have access to the cyberspace domain as technology proliferates
• Cyberspace forces and resources will have the ability to operate continuously (i.e., 24/7/365), providing persistent global and theater effects throughout the spectrum of conflict
• Military operations will continue to depend upon civil, allied, and commercial cyberspace systems and infrastructure
• Sufficient and responsive all-source cyberspace capabilities, ISR systems, infrastructure, and personnel are in place and consistently available to planners, operators, and decision makers
• Policy and legal authorities are in place to enable effective cyberspace operations
• The AF and other Services will organize, train, and equip cyberspace forces, and develop and sustain cyberspace systems, in a de-conflicted and complementary manner3.4 Risks
• An incomplete understanding of friendly and adversarial cyberspace resource uses, capabilities and intent, and their interdependencies, could impact our ability to protect/defend our cyberspace capabilities/assets as well as to counter/affect an adversary’s cyberspace capabilities at the time and place of our choosing
• Failure to plan and employ cyberspace capabilities as an effective means to shape the adversary’s perception, confidence, and tactics, techniques and procedures (TTPs) could result in loss of operational advantages across the range of military operations
• Failure to accurately anticipate and understand technology advances and new capabilities could give an advantage to adversaries, and hinder our ability to adequately react and respond to threats…
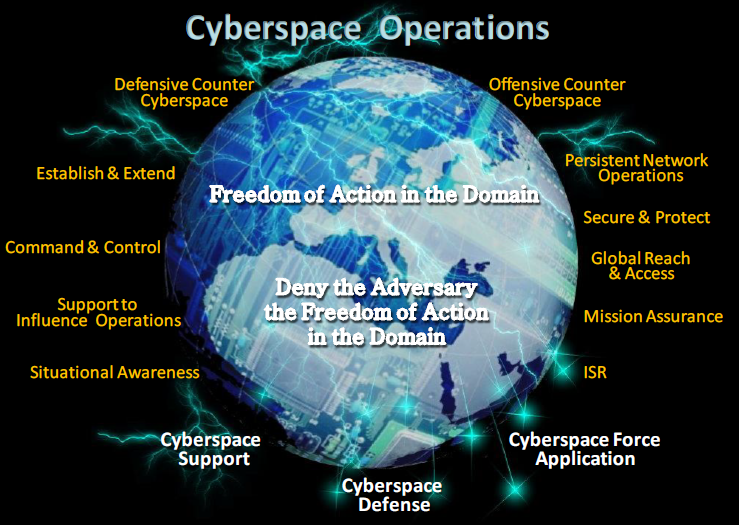
4.1.2 Cyberspace Superiority
Cyberspace Superiority is the operational advantage in, through, and from cyberspace over adversaries to defend, exploit and conduct offensive operations at a given time and place, without effective interference. Joint Test Publication 3-12, Cyberspace Operations
To achieve cyberspace superiority, we must ensure freedom of action in the domain for the joint warfighter, while denying the same advantage to the adversary, at the time and place of our choosing. Freedom of action is achieved by creating and sustaining the access and control of cyberspace infrastructure required for joint operations. This access permits both the movement of data/information, as well as the execution of cyberspace operations by friendly forces. Access may be gained via maneuver, or it may be developed by identifying, acquiring, and sustaining key elements within the domain.
As adversaries become more dependent on the cyberspace domain, our cyberspace operations will be able to deny their ability to organize, coordinate, and conduct effective military operations. These operations may deny, degrade, disrupt, deceive, and/or destroy an adversary’s ability to use the cyberspace domain for his military/warfighting operations. Cyberspace operations may produce physical, lethal, non-lethal, and/or virtual impacts on operations in all other domains. Denying adversary freedom of action in cyberspace requires the ability to identify the key resources they use to gain operational advantage. It is also important to understand that the joint warfighter and adversary may share similar cyberspace infrastructure operated by allied/coalition nations, US Government, private entities, and/or non-combatants. The potential operational impact to attain one outcome may affect other activities.
Achieving cyberspace superiority leads to the following operational advantages:
• The warfighter gains military advantage by executing operations in, through and from cyberspace
• Adversaries are unable to gain and maintain operational advantage derived from their use of cyberspace
• The warfighter has freedom of action to operate in cyberspace without compromising US access to cyberspace
• Cyberspace operations are planned, integrated and closely synchronized with other domain operations to meet warfighter needs and attain the desired outcome(s)…
6.3.2 Attack in Progress
Even with proper safeguards, a determined adversary could successfully launch an attack against the AF cyberspace infrastructure. A primary goal during an attack is to ensure friendly forces maintain the freedom to operate. During a cyberspace attack, network-connected devices and net-enabled applications might be unavailable, and/or their reliability and accuracy would be questionable.
As we ―fight through‖ the attack, cyberspace forces will respond rapidly to limit and combat the attack, and will posture cyberspace resources to support the warfighter. AF cyberspace personnel will possibly initiate a measured response to ensure we maintain the freedom to act in the cyberspace domain.
If an event is determined to be hostile, USSTRATCOM forces enter a heightened state of alert. As directed, cyberspace response forces execute or develop COAs with potential response options. The response option chosen will depend upon, among other things, identifying the source of the attack, the nature of the culpable party (state or non-state actor), the general level of peace or tension between the US and any state or non-state actor, and the impact the attack had on the US national security posture. If this act occurs in nominal/steady state, the response will be politically driven, and the choice of options (military, economic, or diplomatic) will likely reside with the President. There will be some preapproved response options focused on the survivability of cyberspace systems. These preapproved options will be executed, on order, at the tactical level, based on the appropriate attack indications.
If a military response has been authorized, responsibility for planning and executing the response will depend on the situation. For example, when a target in the source AOR is approved, and the AOR commander has sufficient forces in the region to respond, the commander will have responsibility to plan and execute the response. If there are insufficient forces in the region, an alternate commander may be called upon to support the response (e.g., USCYBERCOM). Likewise, USCYBERCOM may conduct joint cyberspace operations necessary to attain and sustain cyberspace control. Global cyberspace operations will be synchronized (e.g., effects-based plans and operations) with regional JFC operations to maximize desired warfighting effects and attain joint military objectives.
6.3.3 Cyberspace Offensive Operations
Cyberspace operations may employ force application in support of combatant commander (CCDR) desired effects. The process begins with a target nomination, or a request, for a desired effect from a combatant command to USSTRATCOM, who in turn will task USCYBERCOM via a fragmentary order (FRAGO). At this point there are three potential options USCYBERCOM could exercise:
6.3.3.1 Cyberspace Offensive Operations – Option 1
USCYBERCOM tasks 24 AF to plan and/or execute a requested operation. In this situation, 24 AF could be tasked to stand up an operational planning team, consisting of appropriate A-staff, subordinate and supporting units to develop the required planning products. The products may include, at a minimum: COAs; CONOPs; employment sustainment schedule; PBA products (high value target [HVT] matrix, adversary COAs, named areas of interest [NAIs], target folders, and assessment criteria); weapon solutions; weapon fact sheet; collateral damage expectation; and intelligence collection plan. The entire planning process is supported by the intelligence community.
Once planning is complete and the decision is made to execute cyberspace warfare operations, the requesting combatant command will engage the Joint Staff/Secretary of Defense (SecDef) and gain authorities to commence offensive operations. USCYBERCOM will validate the target and deconflict/coordinate/ collaborate with interagency organizations, as necessary. Furthermore, USCYBERCOM will develop the cyberspace strike package, schedule the operation, direct the operation, and prepare revisit schedules.
When USCYBERCOM tasks 24 AF to plan/execute the operation, 24 AF, in turn, via its normal operation center processes, tasks subordinate cyberspace warfare units to execute the desired operation. Other cyberspace units will support as directed.
6.3.3.2 Cyberspace Offensive Operations – Option 2
USCYBERCOM could choose to plan the operation and task 24 AF to provide, and/or weaponize, the appropriate tool for their use.
6.3.3.3 Cyberspace Offensive Operations – Option 3
USCYBERCOM exclusively plans and executes the operation with organic assigned forces. There would be no direct 24 AF involvement.
6.4 Post Conflict: Return to Nominal/Steady State Operations
Throughout the network threat/attack phase, cyberspace operators will work to transition resources back to their pre-event operational status. Constantly monitoring and assessing the cyberspace domain will enable the transition to a new steady state. Cyberspace forces will restore any compromised system(s) to operational status in a systematic manner to ensure proper support to AF forces worldwide. Cyberspace defense personnel will remain postured to deter the adversary and maintain positive control over AF cyberspace assets.