This document provides guidance for federal Executive Branch departments and agencies regarding best practices, lessons learned, and recommendations to protect against the threat of malicious unmanned aircraft systems (UAS) operations.
2.0 Background
The development of UAS is a significant technological advance. In addition to recreational and commercial use, unmanned aircraft are used across the United States to support firefighting and search- and-rescue operations, to monitor and assess critical infrastructure, to provide disaster relief by transporting emergency medical supplies to remote locations, and to aid border-security efforts. However, UAS can also be used for malicious schemes by terrorists, criminal organizations (including transnational organizations), and lone actors.
The potential safety hazards and security threats presented by malicious UAS activity in the national airspace system requires security professionals to address the associated risks. Organizations should be aware of the potential exposure of private data through operating UAS. Sensitive data may be at greater risk of exposure when operating UAS designed, manufactured, or supplied abroad where the data is stored, transferred to, or accessible by servers in a foreign country. UAS incorporate technologies that generate or collect sensitive data or otherwise access critical systems.
The ISC details the threat of adversarial use of UAS as an increasing concern in The Design-Basis Threat (DBT) Report. Adversarial uses of UAS include hostile surveillance, smuggling, disruption, and weaponization. From a cybersecurity perspective, an adversary may use UAS as a mobile platform to interrupt or modify digital services or gain unauthorized access to data systems.
The capabilities of UAS continue to grow with longer flight times, greater ranges, and increased payload capacities. These greater capacities, when coupled with malicious intent, increase the threat to federal facilities.
…
5.0 Threats Posed by UAS
The Department of Justice defines credible threat as the reasonable belief based on the totality of circumstances that the activity of a UAV or UAS may, if unabated:
•Cause physical harm to a person;
•Damage property, assets, facilities, or systems;
•Interfere with the mission of a covered facility or asset, including its movement, security, or protection;
•Facilitate or constitute unlawful activity;
•Interfere with the preparation or execution of an authorized government activity, including the authorized movement of persons;
•Result in unauthorized surveillance or reconnaissance; or
•Result in unauthorized access to or disclosure of classified, sensitive, or otherwise lawfully protected information.7
Many UAS events are caused by careless or reckless operators. An adversary can also use UAS in a variety of malicious ways, which include the following:
•Hostile Surveillance. An adversary uses UAS to collect information about federal government operations, security measures, or law enforcement operations.
•Smuggling or Contraband Delivery. An adversary uses UAS to bypass security measures to deliver illegal or prohibited items onto federal property.
•Disruption of Government Business. An adversary uses UAS to interfere with federal government operations through the presence of the UAS, use of on-board cyber-capabilities, or by using the UAS to distribute propaganda onto federal property.
•Weaponization. An adversary mounts a firearm, explosive, chemical, or biological agent ona UAV or deliberately crashes the UAV in an attack.
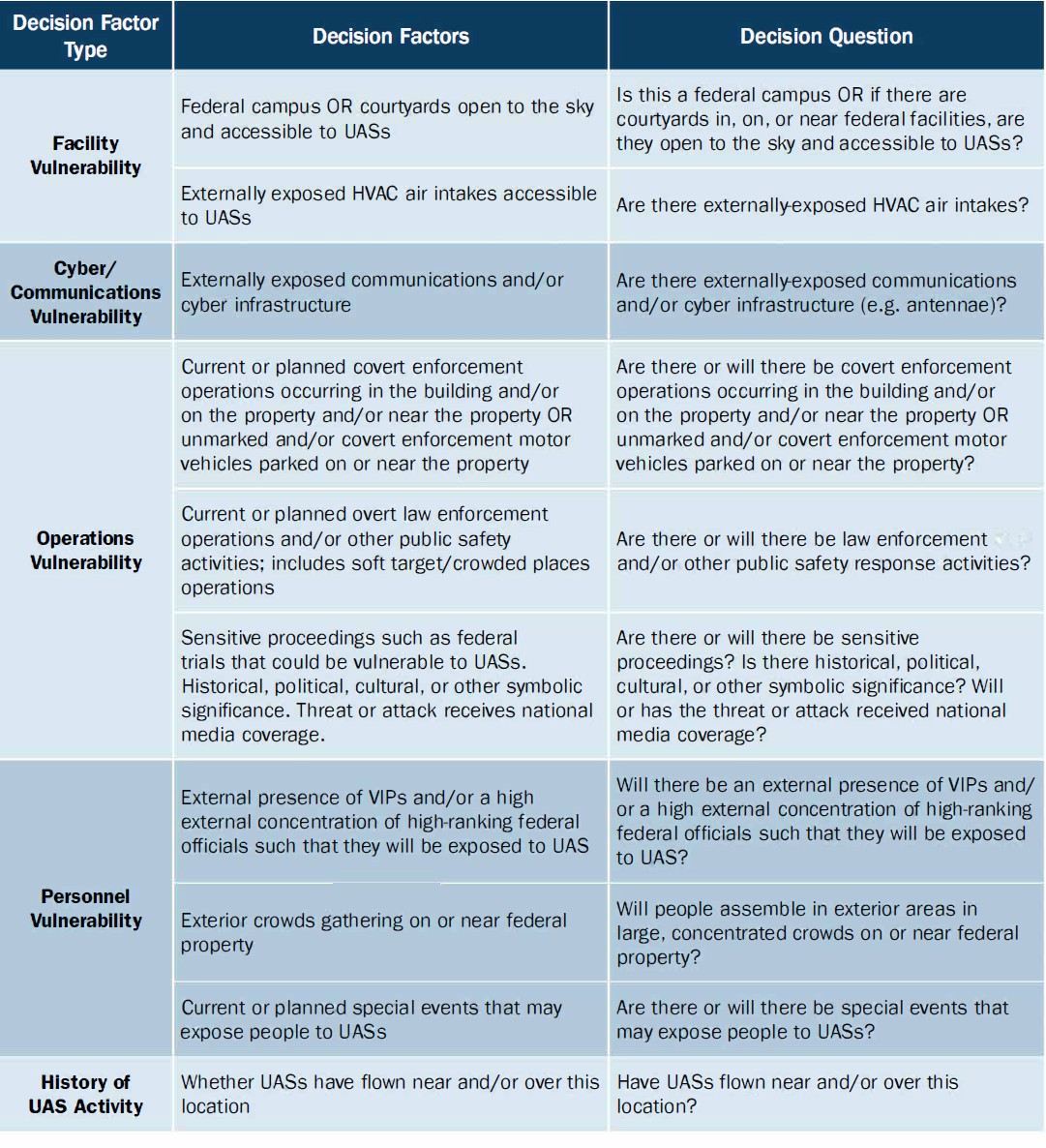
An organization or facility should consider the totality of threats posed by UAS, whether these threats are caused by negligent or reckless use of UAS, criminality, terrorism, or espionage. The risks associated with UAS should not be considered in isolation of other prevailing threat conditions. Considering the full range of threats will facilitate the development of a risk-based mitigation strategy that minimizes those risks most pertinent to the site or organization.
When considering the likelihood of an adversary using UAS, it is important to consider both the intent and the capability of the adversary, including their desired effect. The following table details several basic UAV characteristics structured by the threat actor’s capability level and intended effect.
…