Assuring a Trusted and Resilient Information and Communications Infrastructure
- White House Policy Review
- 76 pages
- Public
The President directed a 60-day, comprehensive, “clean-slate” review to assess U.S. policies and structures for cybersecurity. Cybersecurity policy includes strategy, policy, and standards regarding the security of and operations in cyberspace, and encompasses the full range of threat reduction, vulnerability reduction, deterrence, international engagement, incident response, resiliency, and recovery policies and activities, including computer network operations, information assurance, law enforcement, diplomacy, military, and intelligence missions as they relate to the security and stability of the global information and communications infrastructure. The scope does not include other information and communications policy unrelated to national security or securing the infrastructure. The review team of government cybersecurity experts engaged and received input from a broad cross-section of industry, academia, the civil liberties and privacy communities, State governments, international partners, and the Legislative and Executive Branches. This paper summarizes the review team’s conclusions and outlines the beginning of the way forward towards a reliable, resilient, trustworthy digital infrastructure for the future.
The Nation is at a crossroads. The globally-interconnected digital information and communications infrastructure known as “cyberspace”underpins almost every facet of modern society and provides critical support for the U.S. economy, civil infrastructure, public safety, and national security. This technology has transformed the global economy and connected people in ways never imagined. Yet, cybersecurity risks pose some of the most serious economic and national security challenges of the 21st Century. The digital infrastructure’s architecture was driven more by considerations of interoperability and efficiency than of security. Consequently, a growing array of state and non-state actors are compromising, stealing, changing, or destroying information and could cause critical disruptions to U.S. systems. At the same time, traditional telecommunications and Internet networks continue to converge, and other infrastructure sectors are adopting the Internet as a primary means of interconnectivity. The United States faces the dual challenge of maintaining an environment that promotes efficiency, innovation, economic prosperity, and free trade while also promoting safety, security, civil liberties, and privacy rights.1 It is the fundamental responsibility of our government to address strategic vulnerabilities in cyberspace and ensure that the United States and the world realize the full potential of the information technology revolution.
The status quo is no longer acceptable. The United States must signal to the world that it is serious about addressing this challenge with strong leadership and vision. Leadership should be elevated and strongly anchored within the White House to provide direction, coordinate action, and achieve results. In addition, federal leadership and accountability for cybersecurity should be strengthened. This approach requires clarifying the cybersecurity-related roles and responsibilities of federal departments and agencies while providing the policy, legal structures, and necessary coordination to empower them to perform their missions. While efforts over the past two years started key programs and made great strides by bridging previously disparate agency missions, they provide an incomplete solution. Moreover, this issue transcends the jurisdictional purview of individual departments and agencies because, although each agency has a unique contribution to make, no single agency has a broad enough perspective or authority to match the sweep of the problem.
The national dialogue on cybersecurity must begin today. The government, working with industry, should explain this challenge and discuss what the Nation can do to solve problems in a way that the American people can appreciate the need for action. People cannot value security without first understanding how much is at risk. Therefore, the Federal government should initiate a national public awareness and education campaign informed by previous successful campaigns. Further, similar to the period after the launch of the Sputnik satellite in October, 1957, the United States is in a global race that depends on mathematics and science skills. While we continue to boast the most positive environment for information technology firms in the world, the Nation should develop a workforce of U.S. citizens necessary to compete on a global level and sustain that position of leadership.
…
Near-Term Action Plan
1. Appoint a cybersecurity policy official responsible for coordinating the Nation’s cybersecurity policies and activities; establish a strong NSC directorate, under the direction of the cybersecurity policy official dual-hatted to the NSC and the NEC, to coordinate interagency development of cybersecurity-related strategy and policy.
2. Prepare for the President’s approval an updated national strategy to secure the information and communications infrastructure. This strategy should include continued evaluation of CNCI activities and, where appropriate, build on its successes.
3. Designate cybersecurity as one of the President’s key management priorities and establish performance metrics.
4. Designate a privacy and civil liberties official to the NSC cybersecurity directorate.
5. Convene appropriate interagency mechanisms to conduct interagency-cleared legal analyses of priority cybersecurity-related issues identified during the policy-development process and formulate coherent unified policy guidance that clarifies roles, responsibilities, and the application of agency authorities for cybersecurity-related activities across the Federal government.
6. Initiate a national public awareness and education campaign to promote cybersecurity.
7. Develop U.S. Government positions for an international cybersecurity policy framework and strengthen our international partnerships to create initiatives that address the full range of activities, policies, and opportunities associated with cybersecurity.
8. Prepare a cybersecurity incident response plan; initiate a dialog to enhance public-private partnerships with an eye toward streamlining, aligning, and providing resources to optimize their contribution and engagement
9. In collaboration with other EOP entities, develop a framework for research and development strategies that focus on game-changing technologies that have the potential to enhance the security, reliability, resilience, and trustworthiness of digital infrastructure; provide the research community access to event data to facilitate developing tools, testing theories, and identifying workable solutions.
10. Build a cybersecurity-based identity management vision and strategy that addresses privacy and civil liberties interests, leveraging privacy-enhancing technologies for the Nation.
…
Case for Action
Threats to cyberspace pose one of the most serious economic and national security challenges of the 21st Century for the United States and our allies. A growing array of state and non-state actors such as terrorists and international criminal groups are targeting U.S. citizens, commerce, critical infrastructure, and government. These actors have the ability to compromise, steal, change, or completely destroy information.11 The continued exploitation of information networks and the compromise of sensitive data, especially by nations, leave the United States vulnerable to the loss of economic competitiveness and the loss of the military’s technological advantages. As the Director of National Intelligence (DNI) recently testified before Congress, “the growing connectivity between information systems, the Internet, and other infrastructures creates opportunities for attackers to disrupt telecommunications, electrical power, energy pipelines, refineries, financial networks, and other critical infrastructures.” The Intelligence Community assesses that a number of nations already have the technical capability to conduct such attacks.The growing sophistication and breadth of criminal activity, along with the harm already caused by cyber incidents, highlight the potential for malicious activity in cyberspace to affect U.S. competitiveness, degrade privacy and civil liberties protections, undermine national security, or cause a general erosion of trust, or even cripple society. For example:
• Failure of critical infrastructures. CIA reports malicious activities against information technology systems have caused the disruption of electric power capabilities in multiple regions overseas, including a case that resulted in a multi-city power outage.
• Exploiting global financial services. In November 2008, the compromised payment processors of an international bank permitted fraudulent transactions at more than 130 automated teller machines in 49 cities within a 30-minute period, according to press reports. In another case reported by the media, a U.S. retailer in 2007 experienced data breaches and loss of personally identifiable information that compromised 45 million credit and debit cards.
• Systemic loss of U.S. economic value. Industry estimates of losses from intellectual property to data theft in 2008 range as high as $1 trillion.
…
Anchor Leadership at the White House
Anchoring and elevating leadership for cybersecurity-related policies at the White House signals to the United States and the international community that we are serious about cybersecurity. Many departments and agencies as well as components of the Executive Office of the President (EOP) will need to harmonize disparate responsibilities and authorities to contribute effectively to cybersecurity. Currently, no single individual or entity has the responsibility to coordinate Federal government cybersecurity-related activities. Independent efforts will not be sufficient to address this challenge without a central coordination mechanism, an updated national strategy, an action plan developed and coordinated across the Executive Branch, and the support of Congress.The Administration already has established an Information and Communications Infrastructure Interagency Policy Committee (ICI-IPC), chaired by the National Security Council (NSC) and Homeland Security Council (HSC),19 as the primary policy coordination body for issues related to achieving an assured, reliable, secure, and survivable global information and communications infrastructure and related capabilities.
The President should consider appointing a cybersecurity policy official at the White House, reporting to the NSC and dual-hatted with the NEC, to coordinate the Nation’s cybersecurity-related policies and activities. This individual would chair the ICI-IPC and lead a strong process in consultation with other elements of the EOP to resolve competing priorities and coordinate interagency development of policies and strategies for cybersecurity. The cybersecurity policy official should participate in all appropriate economic, counterterrorism, and science and technology policy discussions to inform them of cybersecurity perspectives.
To be successful, the President’s cybersecurity policy official must have clear presidential support, authority, and sufficient resources to operate effectively in policy formulation and the coordination of interagency cybersecurity-related activities. The cybersecurity policy official should be supported by at least two Senior Directors and appropriate staff from the NSC and at least one Senior Director and appropriate staff from the NEC. These directorates would report through the cybersecurity policy official and work together in pursuit of the goals set forth in this paper and established as national policy. In addition, to achieve additional scale and integration across the NSC, each NSC regional and functional directorate should designate an individual to be responsible for following cybersecurity-related issues in the directorate’s portfolio and coordinating with the directorate for cybersecurity.
The cybersecurity policy official should not have operational responsibility or authority, nor the authority to make policy unilaterally. Using interagency coordination processes, the cybersecurity policy official should harmonize cybersecurity-related policy and technology efforts across the Federal government, ensure that the President’s budget reflects federal priorities for cybersecurity, and develop a legislative agenda, all in consultation with the Federal government’s Chief Technology Officer and Chief Information Officer—along with the appropriate entities within the Office of Management and Budget (OMB), the Office of Science and Technology Policy (OSTP), and the NEC.
…
Improve Partnership Between Private Sector and Government
The Federal government has the responsibility to protect and defend the country, and all levels of government have the responsibility to ensure the safety and well-being of their citizens. The private sector, however, designs, builds, owns, and operates most of the network infrastructures that support government and private users alike. Industry and governments share the responsibility for the security and reliability of the infrastructure and the transactions that take place on it and should work closely together to address these interdependencies. There are various approaches the Federal government could take to address these challenges, some of which may require changes in law and policy.
Private-sector engagement is required to help address the limitations of law enforcement and national security. Current law permits the use of some tools to protect government but not private networks, and vice versa. Industry leaders can help by engaging in enterprise information sharing and account for the corporate risk and the bottom line impacts of data breaches, corporate espionage, and loss or degradation of services. Industry leaders can demand higher assurance from vendors and service providers while taking responsibility to create more secure software and equipment. Businesses need effective means to share detection methods, information about breaches and attack methods, remediation techniques, and forensic capabilities with each other and the Federal government.
…
Finally, the Federal government should engage academia, civil liberties and privacy groups, advocates of open government, and consumers to ensure that government policy adequately considers the broad set of interests that they represent. Few problems can be reduced to a discrete question of process, policy, or technology. Changes in technology often precipitate policy considerations and may require changes in existing processes. Changes in policy (for example, adoption of regulation or tax incentives) can affect decisions regarding procurement or technological research and development. The Federal government could also consider ways in which it could focus more resources on research into possible “game-changing” areas, such as behavioral, policy, and incentive-based cybersecurity solutions. The interwoven nature of these issues underscores the need to ensure that all stakeholders’interests are represented.
…
Partner Effectively With the International Community
International norms are critical to establishing a secure and thriving digital infrastructure. The United States needs to develop a strategy designed to shape the international environment and bring like-minded nations together on a host of issues, including acceptable norms regarding territorial jurisdiction, sovereign responsibility, and use of force. In addition, differing national and regional laws and practices—such as those laws concerning the investigation and prosecution of cybercrime;54 data preservation, protection and privacy; and approaches for network defense and response to cyber attacks—present serious challenges to achieving a safe, secure, and resilient digital environment. Addressing these issues requires the United States to work with all countries— including those in the developing world who face these issues as they build their digital economies and infrastructures—plus international bodies, military allies, and intelligence partners.
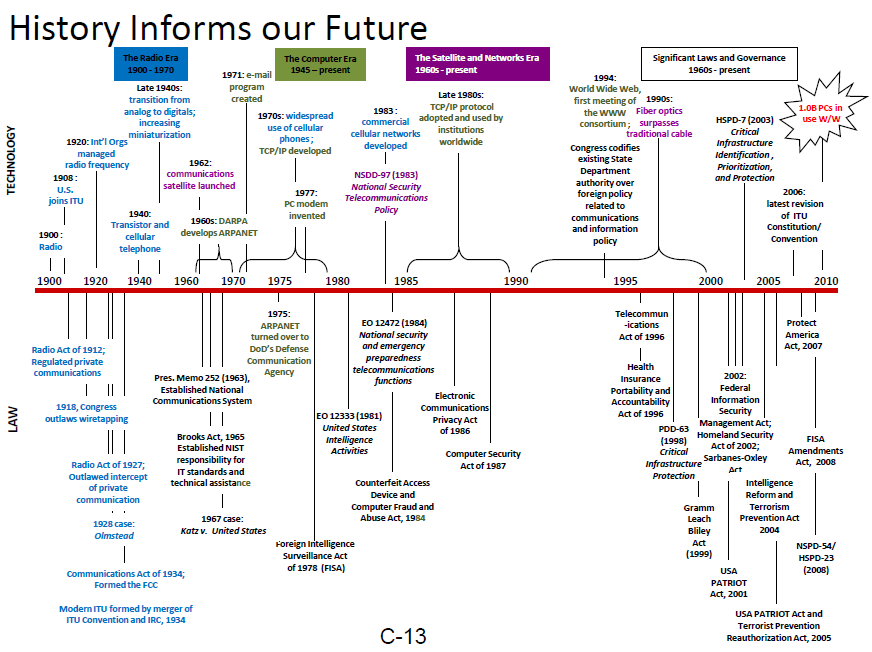
In the past decade, federal communications, infrastructure, and cybersecurity-related policies developed along multiple paths. A more integrated approach to policy formulation would ensure mutually reinforcing objectives and allow the United States to leverage its international opportunities with consistent, more effective positions. The United States should adopt an integrated approach to national interests across a range of substantive areas—including cybersecurity and the protection of free speech and other civil liberties—to develop consistent policies.
The President’s cybersecurity policy official should, working with departments and agencies, strengthen and integrate interagency processes to formulate and coordinate international cybersecurity-related positions. In addition, the Federal government—continuing the long-term history of collaboration with the private sector—should develop a proactive engagement plan for use with international standards bodies. This would include taking stock of current policies and coordinating the development, refinement, or reaffirmation of positions to ensure that the full range of cybersecurity-related economic, national security, public safety, and privacy interests are taken into account.55 More than a dozen international organizations—including the United Nations, the Group of Eight, NATO, the Council of Europe, the Asia-Pacific Economic Cooperation forum, the Organization of American States, the Organization for Economic Cooperation and Development,the International Telecommunication Union(ITU),and the International Organization for Standardization (ISO)—address issues concerning the information and communications infrastructure. New organizations are beginning to consider cybersecurity-related policies and activities, while others are expanding the scope of their existing work. These venues consider policies and conduct activities that sometimes conflict and often overlap. Agreements, standards, or practices promulgated in these organizations have global effects and cannot be ignored. The sheer number, variety, and differing focuses of these venues strain the capacity of many governments, including the United States, to engage adequately.
…
Enhance Information Sharing To Improve Incident Response Capabilities
Information is key to preventing, detecting, and responding to cyber incidents. Network hardware and software providers, network operators, data owners, security service providers, and in some cases, law enforcement or intelligence organizations may each have information that can contribute to the detection and understanding of sophisticated intrusions or attacks. A full understanding and effective response may only be possible by bringing information from those various sources together for the benefit of all.
The Federal government should work with State, local, and tribal governments and the private sector—including data owners, network operators, and experts on privacy and civil liberties—to develop options for cybersecurity-related information sharing that address concerns with privacy and proprietary information and make information sharing mutually beneficial in the national interest. Private companies are concerned about the potential uses of their information. The government must protect privacy rights, law enforcement equities, intelligence sources and methods, and government information that would provide unfair competitive advantages. Clarity and accountability for both government and the private sector are needed to address these concerns. Possible options include:
•Creation of a not-for-profit non-governmental organization to serve as a trusted third-party host where government and private sector information may be shared to enhance the security of critical government and private-sector networks. Such an organization could leverage commercial services without disrupting the growing security service market.
• Continued engagement between the Federal government (e.g., law enforcement agencies) and individual firms or groups of firms—possibly with the participation of State, local, and tribal governments—that could achieve a level of voluntary information sharing within a particular sector or region beyond what could be achieved in a broader setting.
The Administration should consider, in consultation with affected parties and Congress, developing tailored incentives for information sharing. These measures might include, as a last resort, regulatory measures as part of an integrated approach to satisfying society’s interests in robust and resilient critical infrastructures, civil liberties and privacy protections, and maintaining the fair and open economic markets that underlie the U.S. economic system. Privacy enhancing technologies such as encryption or controlled access authentication could ameliorate some risks in sharing information.