 Proposal for Task Z
Proposal for Task Z
- 6 pages
- Confidential
- June 2, 2009
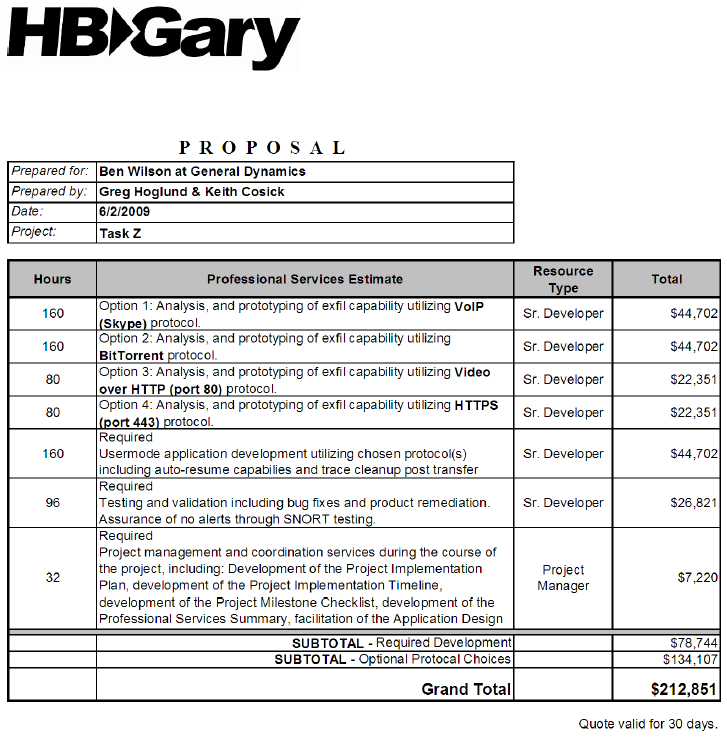
General Dynamics has selected HBGary Inc to provide this proposal for development of a software tool, which provides the user a command line interface, that will enable single file, or full directory exfiltration over TCP/IP. General Dynamics has requested multiple protocols to be scoped as viable options, and this quote contains options for VoIP (Skype) protocol, BitTorrent protocol, video over HTTP (port 80), and HTTPS (port 443). HBGary will research and analyze the best solution given the client’s choice of protocol(s). As outlined in the Bill of Materials on page 4 of this document, cost per protocol is provided separately, and one or more of the options can be chosen by General Dynamics. HBGary will develop this user mode application with listen capabilities, trace cleanup, and ensure network sniffer testing doesn’t trigger any alerts. The application will be provided for user testing, and validation at the close of the development cycle which will be scheduled jointly between HBGary, and General Dynamics.
Primary Objectives:
• Development of a user mode application that will enable file or directory exfiltration over TCP/IP utilizing one or more protocols to be selected by General Dynamics
• Application has listen (server) side, auto resume capabilities and file/read/exfil loop inclusion
• As part of final validation, HBGary will ensure SNORT/Wireshark testing returns no alerts…