A slide from a FEMA presentation describes some of the key details regarding National Level Exercise 2012.
Public Intelligence
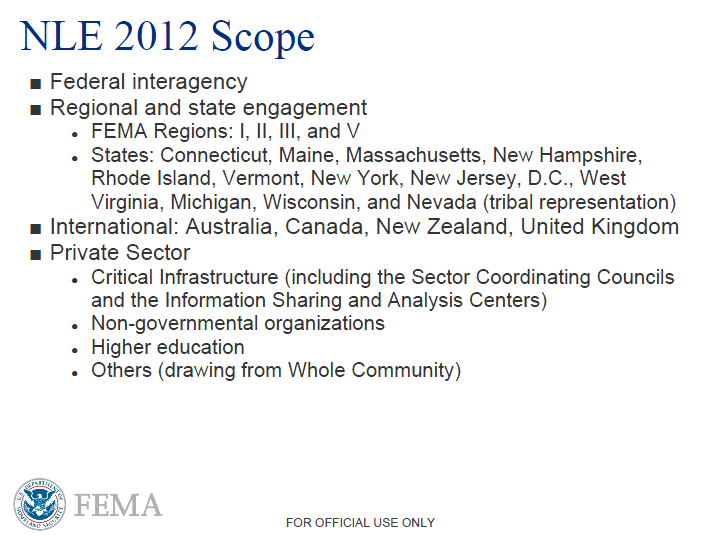
Rather than combating natural disasters or a nuclear detonation in a major U.S. city, this year’s National Level Exercise will focus on cyber threats to critical infrastructure and the “real world” implications for government and law enforcement of large-scale cyber attacks. National Level Exercise 2012 (NLE 2012) is scheduled to take place in June and will involve emergency response personnel from at least thirteen states, four countries, nearly every major governmental department as well as a number of private companies, non-governmental organizations, institutions of higher education and local fusion centers. The exercise will span four FEMA regions and will include scenarios affecting the National Capital Region.
Past NLEs have focused primarily on threats related to terrorism or catastrophic natural disasters. NLE 2010 focused on the hypothetical detonation of an improvised nuclear device (IND) in Las Vegas. NLE 2011 concerned a massive earthquake occurring in the New Madrid Seismic Zone. NLE 2012 will be the first exercise in the series to concern itself primarily with cyber threats. A private sector participant guide released by FEMA states that NLE 2012 “will address cyber and physical response coordination, including resource allocation . . . emergency assistance and disaster relief resources, relative to a cyber event with physical effects.” Another presentation from FEMA adds that the exercise will evaluate government “roles and responsibilities in coordinating national cyber response efforts and their nexus with physical response efforts.”
While the exact scenario for NLE 2012 is not known, the “high level” goals include simulating a situation where there is an “ambiguous threat landscape with multiple adversary types” that produces “physical impacts resulting from cyber attack and cascading effects” that threaten “critical commercial logistics and data, industrial control systems, and associated operations.” NLE 2012 will be unique in that there “will be an emphasis on the shared responsibility among the Federal Government; state, local, tribal nations, and territories; the private sector; and international partners to manage risk in cyberspace and respond together to a cyber event with national consequences.” Due to the “sensitivity of the exercise scenario and the related private sector concerns in terms of media exposure” FEMA has made it clear that the names of private sector participants will not be publicly released.
The exercise will occur amidst a growing climate of panic in Washington regarding the state of U.S. cybersecurity. The FBI’s top cybersecurity official recently resigned stating that the U.S. is fighting a losing war against hackers: “I don’t see how we ever come out of this without changes in technology or changes in behavior, because with the status quo, it’s an unsustainable model. Unsustainable in that you never get ahead, never become secure, never have a reasonable expectation of privacy or security.” Former government officials are advocating U.S. Customs “inspect what enters and exits the United States in cyberspace” and calling for prompt action on multiple pieces of cybersecurity legislation passing through the House and Senate.
NLE 2012’s goal of examining physical effects of cyber attacks underscores a comment recently made by the director of the FBI that the “cyber threat” will soon replace terrorism as the country’s highest national security priority. In March, a multi-agency exercise that included the FBI and NSA simulated a cyber attack capable of crippling the New York power grid during a summer heat wave. Last September, the Department of Homeland Security issued a warning to members of the “critical infrastructure community” that the hacktivist group Anonymous had expressed interest in industrial control systems. Computer security researchers have also recently demonstrated a number of techniques for attacking computer systems used in critical infrastructure that reportedly resemble the Stuxnet virus responsible for disrupting Iran’s nuclear program in 2010.
