 Multi-Jurisdiction IED Security Plan—Planning Guide
Multi-Jurisdiction IED Security Plan—Planning Guide
- 36 pages
- For Official Use Only
- July 2008
Executive Summary
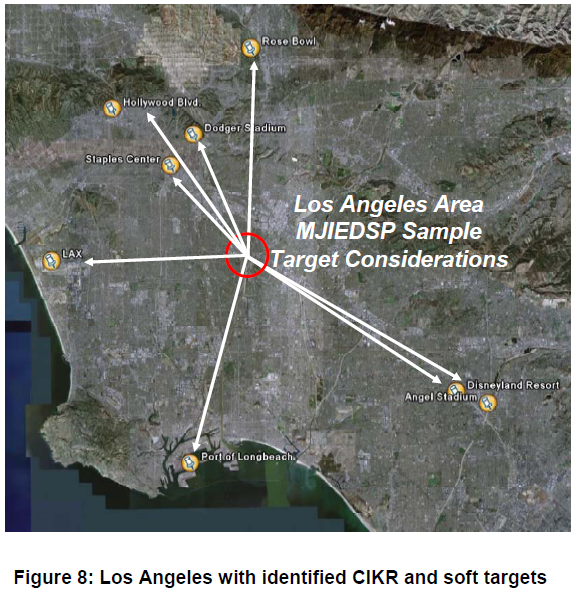
The Multi-Jurisdiction Improvised Explosive Device (IED) Security Plan (MJIEDSP) Planning Guide assists multi-jurisdiction areas in developing a detailed IED security plan. The IED security plan outlines specific bombing prevention actions that reduce vulnerability and mitigate risk against the primary terrorist IED attack method within a multi-jurisdiction area.
The IED Threat
Improvised Explosive Devices (IEDs) are a preferred method of attack for terrorists around the world. IEDs are relatively simple to assemble and employ, and provide terrorists with an operational flexibility that poses great challenges for those responsible with preventing their use or mitigating their effects. Furthermore, the tactics that terrorists use to employ IEDs are continually evolving. Suicide bombers, vehicle-borne devices, simultaneous and coordinated attacks, and the targeting of emergency responders with secondary devices are a few of the creative methods terrorists use to increase the disruption and fear caused by IEDs.
IED Security
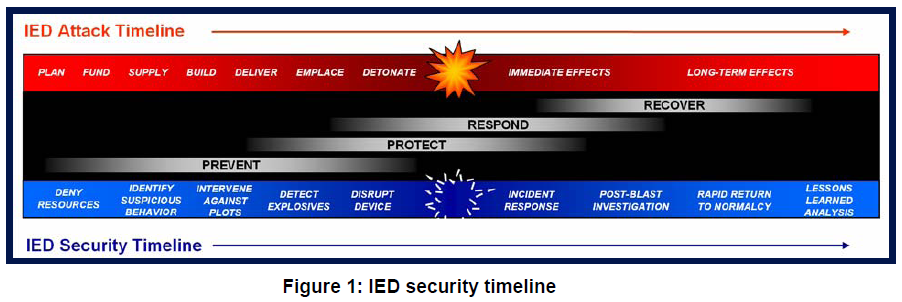
“IED security” is defined as the condition wherein the risk posed by IED attacks is managed to the greatest extent possible. Achieving IED security within a multi-jurisdiction area requires a properly balanced approach that encompasses the efforts of all those working to apply law enforcement, protective measures, and emergency response resources, across the continuum of homeland security missions—prevention, protection, response, and recovery. While acknowledging the importance of each mission area, this guide emphasizes the development of actions multi-jurisdictions should take during the prevention and protection stages of IED security.
MJIEDSP Development
The development of a MJIEDSP is a cooperative effort requiring the collaboration of numerous agencies across multiple localities, disciplines, and levels of government. The development methodology includes a 10-step process to be completed jointly through the accompanying MJIEDSP template. As planning partners read through this guide, outputs are identified for each step, which the planner will then complete by filling out specific sections within the template. Together, both documents guide the planner in determining key threats and vulnerabilities, and finally in developing a plan that identifies specific steady-state and threat-initiated actions to reduce the risk of an IED attack to their primary area of operations. Both the initial plan and security partnerships can and should be expanded using this repeatable process to further define and improve IED security actions within the planning area.
…