 National Counterterrorism Center’s Weapons, Tactics, and Targets Group
National Counterterrorism Center’s Weapons, Tactics, and Targets Group
- 6 pages
- For Official Use Only
- August 12, 2010
(U) Scope
(U//FOUO) This Note supplements the 10 June 2010 DHS Note titled Webcams: Potential Terrorist and Criminal Surveillance Tool. The National Counterterrorism Center and DHS/Office of Intelligence and Analysis are releasing this Note to provide perspective and understanding of the nature of the threat and to assist federal, state, local, and tribal government agencies, the private sector, and other entities in their efforts to develop protective and support measures relating to this preoperational surveillance method.
(U) Overview
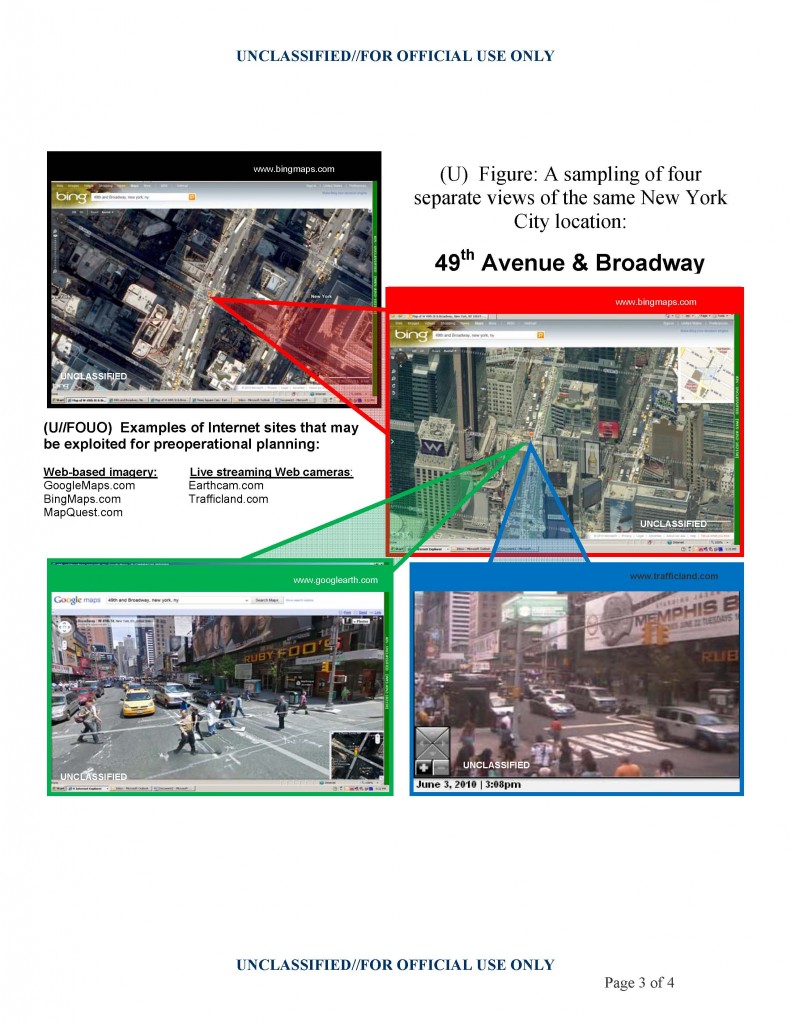
(U//FOUO) Detailed video obtained through live Web-based camera feeds combined with street-level and direct overhead imagery views from Internet imagery sites allow terrorists to conduct remote surveillance of multiple potential targets without exposing themselves to detection.
— (U//FOUO) As early as 2006, insurgents used a mapping capability operated by GoogleUSPER, called “GoogleEarth,” for tactical planning of rocket attacks against U.S. military targets in Iraq, according to open source reporting.
(U//FOUO) The increasing sophistication of these commercially available Internet tools may allow terrorists to study security measures in place and the relationship between the target and surrounding area using various viewing angles, to choose ingress and egress routes, and to monitor attack progress and results. Individually each system has strengths and weaknesses, but combining the use of multiple Internet tools can provide detailed, real-time information on potential attack locations (see figure on page 3). By minimizing their physical presence during the target selection and surveillance phases, terrorists may limit law enforcement’s ability to detect and disrupt any plot.
(U) Supplemental Measures
(U//FOUO) Below are several supplemental measures that could reduce vulnerabilities to online surveillance:
— (U//FOUO) Security personnel need to be aware of camera coverage and ensure that protective measures are not predictable.
— (U//FOUO) Conduct a self-analysis of local facilities and transportation routes from an adversary’s perspective by periodically reviewing Internet imagery sites to identify possible vulnerabilities visible to outside parties.
— (U//FOUO) Screen static security measures from line-of-sight or overhead view using physical concealment such as fences, walls, roofs, and foliage.
— (U//FOUO) Place additional security measures outside of webcam or street-level view.
— (U//FOUO) Vary the schedule and placement of security personnel.
— (U//FOUO) Establish mobile checkpoints to supplement static sites.…