This report examines the substantial economic costs that malicious cyber activity imposes on the U.S. economy. Cyber threats are ever-evolving and may come from sophisticated adversaries. Due to common vulnerabilities, instances of security breaches occur across firms and in patterns that are difficult to anticipate. Importantly, cyberattacks and cyber theft impose externalities that may lead to rational underinvestment in cybersecurity by the private sector relative to the socially optimal level of investment. Firms in critical infrastructure sectors may generate especially large negative spillover effects to the wider economy. Insufficient data may impair cybersecurity efforts. Successful protection against cyber threats requires cooperation across firms and between private and public sectors.
Overall:
• We estimate that malicious cyber activity cost the U.S. economy between $57 billion and $109 billion in 2016.
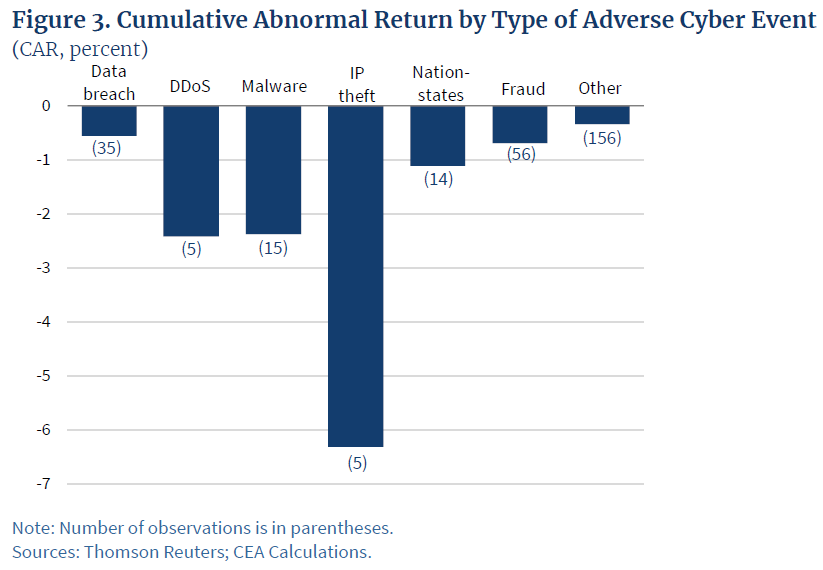
• Malicious cyber activity directed at private and public entities manifests as denial of service attacks, data and property destruction, business disruption (sometimes for the purpose of collecting ransoms) and theft of proprietary data, intellectual property, and sensitive financial and strategic information.
• Damages from cyberattacks and cyber theft may spill over from the initial target to economically linked firms, thereby magnifying the damage to the economy.
• Firms share common cyber vulnerabilities, causing cyber threats to be correlated across firms. The limited understanding of these common vulnerabilities impedes the development of the cyber insurance market.
• Scarce data and insufficient information sharing impede cybersecurity efforts and slow down the development of the cyber insurance market.
• Cybersecurity is a common good; lax cybersecurity imposes negative externalities on other economic entities and on private citizens. Failure to account for these negative externalities results in underinvestment in cybersecurity by the private sector relative to the socially optimal level of investment.
• Cyberattacks against critical infrastructure sectors could be highly damaging to the U.S. economy.
…
According to government and industry sources, malicious cyber activity is a growing concern for both the public and private sectors. Between 2013 and 2015, according to the Office of the Director of National Intelligence (DNI), cyber threats were the most important strategic threat facing the United States (DOD 2015a)—they “impose costs on the United States and global economies” and present “risks” for “nearly all information, communication networks, and systems” (DNI 2017). Cyber threat actors fall into six broad groups, each driven by distinct objectives and motivations:
Nation-states: The main actors are Russia, China, Iran, and North Korea, according to DNI (2017). These groups are well funded and often engage in sophisticated, targeted attacks. Nation-states are typically motivated by political, economic, technical, or military agendas, and they have a range of goals that vary at different times. Nation-states frequently engage in industrial espionage. If they have funding needs, they may conduct ransom attacks and electronic thefts of funds. Nation-states frequently target PII in order to spy on certain individuals. Furthermore, per our interviews of cybersecurity experts, nation-states may engage in business destruction involving one or more firms, potentially as a retaliation against sanctions or other actions taken by the international community.
Corporate competitors: These are firms that seek illicit access to proprietary IP, including financial, strategic, and workforce-related information on their competitors; many such corporate actors are backed by nation-states.
Hacktivists: These are generally private individuals or groups around the globe who have a political agenda and seek to carry out high-profile attacks. These attacks help hacktivists distribute propaganda or to cause damage to opposition organizations for ideological reasons.
Organized criminal groups: These are criminal collectives that engage in targeted attacks motivated by profit seeking.2 They collect profits by selling stolen PII on the dark web and by collecting ransom payments from both public and private entities by means of disruptive attacks.
Opportunists: These are usually amateur hackers driven by a desire for notoriety.
Opportunists typically attack organizations using widely available codes and techniques, and thus usually represent the least advanced form of adversaries.
Company insiders: These are typically disgruntled employees or ex-employees looking for revenge or financial gain. Insiders can be especially dangerous when working in tandem with external actors, allowing these external actors to easily bypass even the most robust defenses.
…