This document describes the Vulnerabilities Equities Policy and Process for departments and agencies of the United States Government (USG) to balance equities and make determinations regarding disclosure or restriction when the USG obtains knowledge of newly discovered and not publicly known vulnerabilities in information systems and technologies. The primary focus of this policy is to prioritize the public’s interest in cybersecurity and to protect core Internet infrastructure, information systems, critical infrastructure systems, and the U.S. economy through the disclosure of vulnerabilities discovered by the USG, absent a demonstrable, overriding interest in the use of the vulnerability for lawful intelligence, law enforcement, or national security purposes.
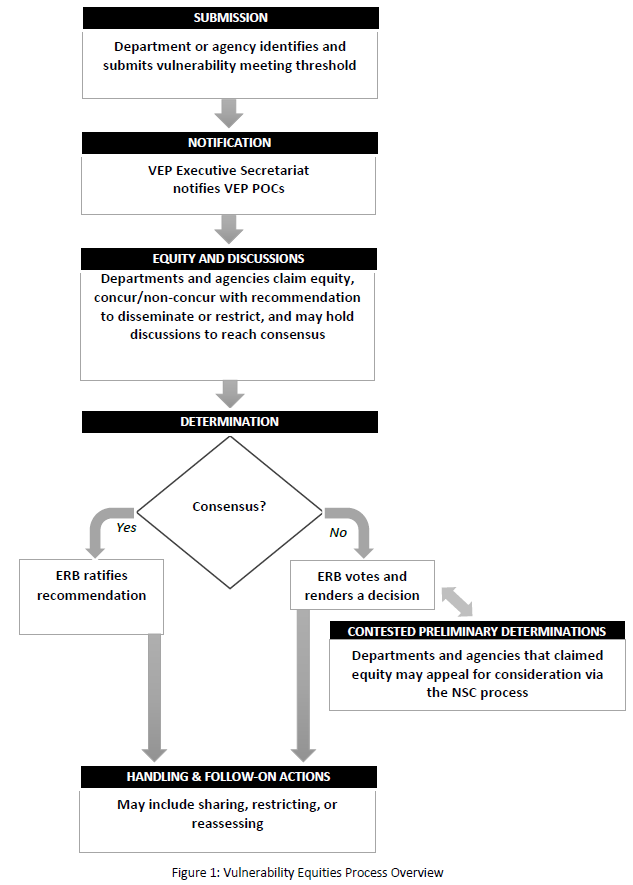
The Vulnerabilities Equities Process (VEP) balances whether to disseminate vulnerability information to the vendor/supplier in the expectation that it will be patched, or to temporarily restrict the knowledge of the vulnerability to the USG, and potentially other partners, so that it can be used for national security and law enforcement purposes, such as intelligence collection, military operations, and/or counterintelligence. The U.S. Government’s determination as to whether to disseminate or restrict a vulnerability is only one element of the vulnerability equities evaluation process and is not always a binary determination. Other options that can be considered include disseminating mitigation information to certain entities without disclosing the particular vulnerability, limiting use of the vulnerability by the USG in some way, informing U.S. and allied government entities of the vulnerability at a classified level, and using indirect means to inform the vendor of the vulnerability. All of these determinations must be informed by the understanding of risks of dissemination, the potential benefits of government use of the vulnerabilities, and the risks and benefits of all options in between. This document defines the policy and process for evaluating competing considerations to inform U.S. Government decisions.
…
4.1. Equities Review Board and VEP Director
The Equities Review Board (ERB) is the primary forum for interagency deliberation and determinations concerning the VEP. The ERB will meet monthly, but may also be convened sooner if an immediate need arises.
The ERB will consist of representatives from the following agencies who are authorized to represent the views of their respective agency head:
- Office of Management and Budget
- Office of the Director of National Intelligence (to include Intelligence Community-Security Coordination Center (IC-SCC))
- Department of the Treasury
- Department of State
- Department of Justice (to include the Federal Bureau of Investigation and the National Cyber Investigative Joint Task Force (NCIJTF))
- Department of Homeland Security (to include the National Cybersecurity Communications and Integration Center (NCCIC) and the United States Secret Service (USSS))
- Department of Energy
- Department of Defense (including the National Security Agency (NSA) (including Information Assurance and Signals Intelligence elements)), United States Cyber Command, and DoD Cyber Crime Center (DC3))
- Department of Commerce
- Central Intelligence Agency
Other USG agencies may participate when demonstrating responsibility for, or identifying equity in, a vulnerability under deliberation. Changes to the name of an agency will not affect its participation in this process.
Each agency participating in the VEP will designate an agency point of contact (POC) to act as the focal point for vulnerability submissions for their respective organization and the primary contact for the VEP Executive Secretariat.
The VEP POC will ensure one or more Subject Matter Experts (SME) from their agency are identified to support equities determinations and discussions as needed.
The VEP Director at the NSC will be responsible for ensuring effective implementation of VEP policies. The VEP Director is the Special Assistant to the President and Cybersecurity Coordinator, or an equivalent successor.
…