For more information on the following proposal, see Ars Technica’s article “Verisign wants power to shut sites down upon law enforcement request” with excellent criticisms from the ACLU and EFF.
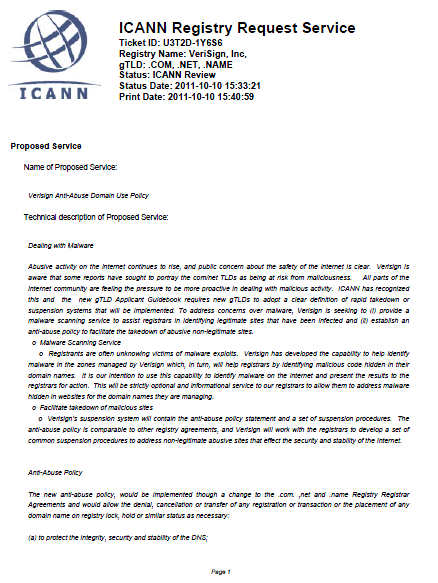
Verisign Anti-Abuse Domain Use Policy
- 10 pages
- October 10, 2011
Dealing with Malware
Abusive activity on the internet continues to rise, and public concern about the safety of the internet is clear. Verisign is aware that some reports have sought to portray the com/net TLDs as being at risk from maliciousness. All parts of the internet community are feeling the pressure to be more proactive in dealing with malicious activity. ICANN has recognized this and the new gTLD Applicant Guidebook requires new gTLDs to adopt a clear definition of rapid takedown or suspension systems that will be implemented. To address concerns over malware, Verisign is seeking to (i) provide a malware scanning service to assist registrars in identifying legitimate sites that have been infected and (ii) establish an anti-abuse policy to facilitate the takedown of abusive non-legitimate sites.
Malware Scanning Service
- Registrants are often unknowing victims of malware exploits. Verisign has developed the capability to help identify malware in the zones managed by Verisign which, in turn, will help registrars by identifying malicious code hidden in their domain names. It is our intention to use this capability to identify malware on the internet and present the results to the registrars for action. This will be strictly optional and informational service to our registrars to allow them to address malware hidden in websites for the domain names they are managing.
- Facilitate takedown of malicious sites
- Verisign’s suspension system will contain the anti-abuse policy statement and a set of suspension procedures. The anti-abuse policy is comparable to other registry agreements, and Verisign will work with the registrars to develop a set of common suspension procedures to address non-legitimate abusive sites that effect the security and stability of the Internet.
Anti-Abuse Policy
The new anti-abuse policy, would be implemented though a change to the .com. ,net and .name Registry Registrar Agreements and would allow the denial, cancellation or transfer of any registration or transaction or the placement of any domain name on registry lock, hold or similar status as necessary:
(a) to protect the integrity, security and stability of the DNS;
(b) to comply with any applicable court orders, laws, government rules or requirements, requests of law enforcement or other governmental or quasi-governmental agency, or any dispute resolution process;
(c) to avoid any liability, civil or criminal, on the part of Verisign, as well as its affiliates, subsidiaries, officers, directors, and employees;
(d) per the terms of the registration agreement,
(e) to respond to or protect against any form of malware (defined to include, without limitation, malicious code or software that might affect the operation of the Internet),
(f) to comply with specifications adopted by any industry group generally recognized as authoritative with respect to the Internet (e.g., RFCs),
(g) to correct mistakes made by Verisign or any Registrar in connection with a domain name registration, or
(h) for the non-payment of fees to Verisign. Verisign also reserves the right to place upon registry lock, hold or similar status a domain name during resolution of a dispute;
Malware Scanning Service
In connection with the adoption of the anti-abuse police, Verisign provide malware scanning for all .com, net and .name registrars pursuant to section 2.7 (b) of the proposed .com,.net .name Registry Agreements. This service will be optional allowing registrars to opt out of the service for .com, .net, and .name domain names under their management.
Section 2.7(b) provides:
If Registrar elects to allow Verisign to scan for malware, then in its registration agreement with each Registered Name Holder, Registrar shall also require such Registered Name Holder to acknowledge and agree that Verisign reserves the right for it or its agent to perform, in Verisign’s unlimited and sole discretion, website scans or other views of websites for the purposes of, and only to the extent necessary to such purposes, detecting malware or as necessary protecting the integrity, security or stability of the registry; provided, Verisign will not disclose except to registrant and/or Registrar any data collected pursuant to a scan other than as permitted by applicable law, including applicable privacy and data protection laws, or pursuant to a court order.
Verisign defines malware as
“Malware” means any programming (code, scripts, active content, or other computer instruction or set of computer instructions) designed, or is intended, to (a) block access to, prevent the use or accessibility of, or alter, destroy or inhibit the use of, a computer, computer program, computer operations, computer services or computer network, by authorized users; (b) adversely affect, interrupt or disable the operation, security, or integrity of a computer, computer program, computer operations, computer services or computer network; (c) falsely purport to perform a useful function but which actually perform a destructive or harmful function or perform no useful function but consume significant computer, telecommunications or memory resources; (d) gain unauthorized access to or use of a computer, computer program, computer operations, computer services or computer network; (e) alter, damage, destroy, monitor, collect or transmit information within a computer, computer program, computer operations, computer services or computer network without the authorization of the owner of the information; (f) usurp the normal operation of a computer, computer program, computer operations, computer services or computer network; or (g) other abusive behavior. Malware includes, without limitation, various forms of crimeware, dialers, disabling devices, dishonest adware, hijackware, scareware, slag code (logic bombs), rootkits, spyware, Trojan horses, viruses, web bugs, and worms.