San Diego Police Department
- 55 pages
- Law Enforcement Sensitive
- September 21, 2009
Gang Intelligence
• What happens when an investigator leaves the unit…? Information goes with him!
• We are missing a boat load of data – Wire Conversations, Pen Registers, LPR…
• Lack the ability to data mineIN EFFECT WE ARE DATA RICH BUT INFORMATION POOR
…
ILP: Products
• Strategic Intelligence: Helps decision makers define a vision and hold managers accountable.
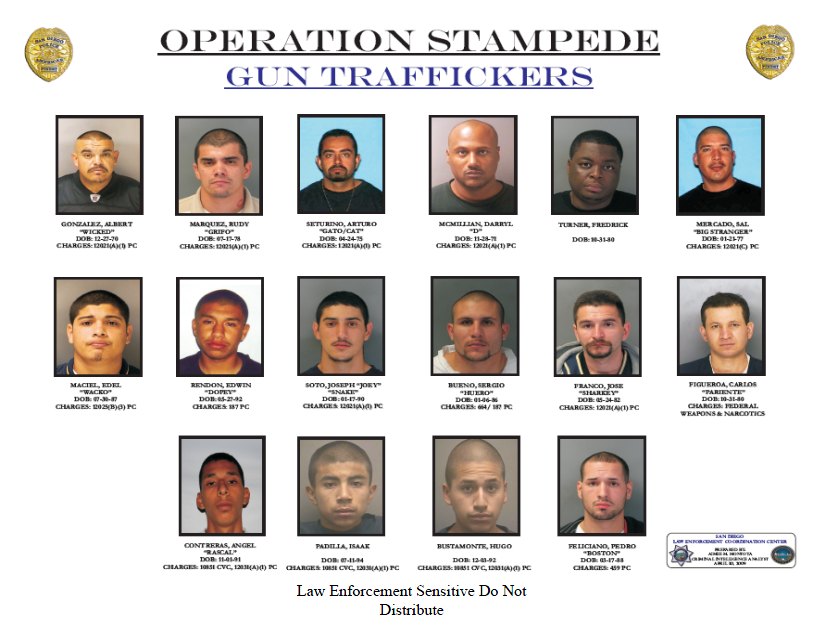
• Operational Intelligence: Gives managers adequate information to develop operational plans and adjust resources.
• Tactical Intelligence: Allows line personnel the ability to focus their efforts on solving problems and targeting the right people.…
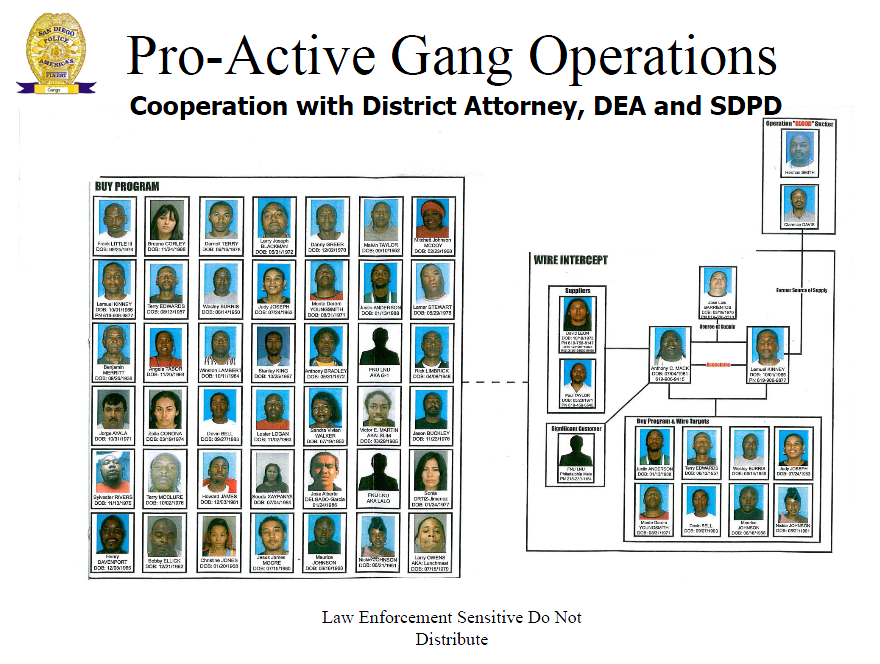
Wire Intercepts/Technology
• Pen Registers: Hundreds of phone numbers, times, dates and locations
• Intercepts: Conversations, names, location, key words, language
• MySpace, Facebook, Bebo, Know Gangs,
• Cell phone downloader
• CCTV (Multiple sources)
• Bio-Metrics…
Data Mining
• ISYS: Searches all CRMS reports, F.I.’s, Arrests, in a Google search format
• PD Intel Database: A custom built intelligence database that allows detectives to access all CI debriefings in a searchable format. (being built)
• CalGang, Gangnet, RISS, COPLink, NINCrime Analysis
• GIS Mapping Systems
• Hot Spot Identification
• Series Identification
• Research Environmental Criminology
• Develop visual representations of crime problems
• Research expert into what works
• Statistical probability
• Not a crime accounting unit!…
Open Source/Research
• Hundreds of sources: Media (Papers, TV, Cable, Industry Associations)
• Academic Papers: DOJ, Cal DOJ, PERF
• Other Governments: Home Office, Australia, New Zealand (ILP) and others…