This document was first released publicly by Anonymous on the AntiSec Embassy, an anonymously hosted website accessible via the Tor network.
TC 2-33.4 Intelligence Analysis
- 160 pages
- For Official Use Only
- June 2009
- 3.19 MB
THE OPERATIONAL ENVIRONMENT
America has entered an era of persistent conflict where states, nations, transnational actors, and nonstate actors are increasingly willing to use violence to achieve their political and ideological ends. These entities will continue to challenge and redefine the global distribution of power, the concept of sovereignty, and the nature of warfare. Globalization, technology, population growth, urbanization, and demand for natural resources are creating an environment where the location of the next crisis requiring American intervention is not always predictable. Generally with little notice, Army units will be employed in complex and multidimensional environments; usually fought in urban terrain among noncombatant populations. Additionally, they will be called on to conduct full spectrum operations as part of an interdependent joint force conducting simultaneous offensive, defensive, and stability operations. See FM 3-0 for a detailed description of the operational environment.
THE THREAT ENVIRONMENT
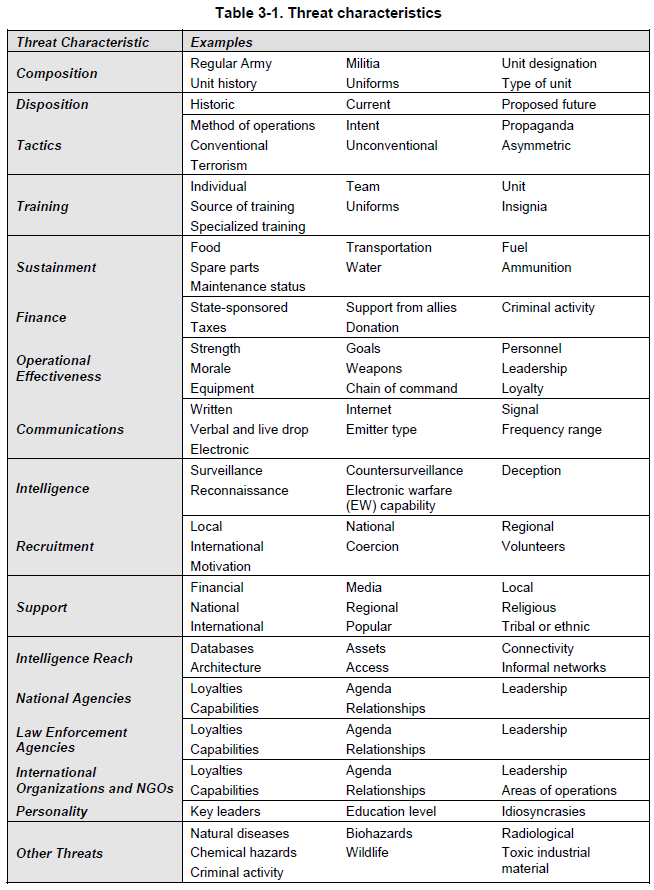
FM 3-0 defines threats as nation-states, organizations, people, groups, conditions, or natural phenomena able to damage or destroy life, vital resources, or institutions. There are four major threat categories intelligence analysts must assist the commander and staff in understanding:
• Irregular threats are characterized as entities seeking to erode U.S. power through protracted struggle. Radical fundamentalists, transnational terrorists, and guerrilla forces are examples of irregular threat. These groups will employ unconventional and asymmetric methods and means to counter U.S. advantages. Irregular warfare includes terrorism, insurgency, and guerilla warfare.
• Traditional threats emerge from states employing recognized military capabilities and forces in understood forms of military competition and conflict.
• Catastrophic threats involve the acquisition, possession, and use of chemical, biological, radiological, nuclear, and high-yield explosives (CBRNE) weapons.
• Disruptive threats involve an enemy using new technologies to reduce U.S. advantages in key operational domains.Army units are likely to face any combination of these threats when deployed. By combining irregular, traditional, catastrophic, and disruptive capabilities, adversaries will seek to create advantageous conditions by changing the nature of the conflict from one where U.S. forces can effectively use size, firepower, and technology to its advantage to one where adversaries can use low technology solutions and control of key and decisive terrain to gain and maintain the initiative.
U.S. forces may be employed under the following five types of operational themes across the spectrum of conflict; each with its own unique threat environment:
• Peacetime military engagement comprises all military activities that involve other nations and are intended to shape the security environment in peacetime. Examples include multinational training exercises, security assistance, joint combined exchange training, recovery operations, arms control, and counterdrug operations. Combat is not likely during these operations, but terrorist attacks are always possible and force protection and operations security (OPSEC) are major concerns.
• Limited interventions are executed to achieve an end state that is clearly defined and limited in scope. They are normally conducted by joint task forces. Examples of limited interventions are noncombatant evacuation, raids, show of force, foreign humanitarian assistance, consequence management, sanction enforcement, and elimination of weapons of mass destruction (WMDs). Like peacetime military engagement, combat is not likely. However, the threat of terrorist attacks is possible, as are attacks from the general population. Force protection, OPSEC, and targeting operations are major concerns.
• Peace operations is a broad term that encompasses multiagency and multinational crisis response and limited contingency operations. The primary purpose of peace operations is to create a safe and secure environment, deter adversaries from overt actions against each other, and provide time for civilian agencies to generate a self-sustaining peace. Peace operations include peacekeeping, peace building, peacemaking, peace enforcement, and conflict prevention. Peace operations normally occur in complex environments. They are characterized by asymmetric threats, a failing government, absence of the rule of law, terrorism, human rights abuses, collapse of civil infrastructure, and the presence of dislocated civilians. Attacks by insurgent and terrorist groups are likely, and U.S. forces may conduct limited offensive operations against these groups in support of stability operations.
• Irregular warfare is a violent struggle among state and nonstate actors for legitimacy and influence over a population. It differs from conventional operations in two aspects. First, it is warfare among and within the people. Second, it emphasizes an indirect approach. Irregular warfare avoids direct military confrontation. Instead, it combines irregular forces and indirect unconventional methods to exhaust the opponent. Types of operations U.S. forces may be employed in to counter irregular warfare are foreign internal defense, support to insurgency, counterinsurgency (COIN), combating terrorism, and unconventional warfare. Traditionally, these missions are conducted by special forces. However, if special forces and host-nation (HN) forces cannot defeat unconventional and irregular threats, conventional Army forces can assume the lead role. Operation Iraqi Freedom and Operation Enduring Freedom are good examples of this.
• Major combat operations occur in circumstances usually characterized by general war and combat between large formations. In this instance, U.S. forces are normally involved in offensive or defensive operations as part of a larger joint force. Major combat operations are the operational theme for which doctrine, including the principles of war, was originally developed. The intelligence analyst provides doctrinal intelligence support to major combat operations in accordance with FM 2-0.…
THE INTELLIGENCE WARFIGHTING FUNCTION
1-1. The intelligence warfighting function is the related tasks and systems that facilitate understanding of the operational environment, enemy, terrain, and civil considerations (FM 3-0). It includes tasks associated with intelligence, surveillance, and reconnaissance (ISR) operations, and is driven by the commander. Intelligence is more than just collection. It is a continuous process that involves analyzing information from all sources and conducting operations to develop the situation. The intelligence warfighting function is comprised of the following four primary Army intelligence tasks that facilitate the commander’s visualization and situational understanding of the operational environment:
- Support to force generation.
- Support to situational understanding.
- Perform intelligence, surveillance, and reconnaissance.
- Support to targeting and information superiority.
1-2. Intelligence analysis is a process that is focused by the tasks established by the intelligence warfighting function and described in FM 2-0. Intelligence analysts at all levels must understand the task and purpose of the intelligence warfighting function, be proficient in the subtasks articulated in FM 2-0, and know how intelligence analysis relates to military planning and operations. See FM 2-0 for a detailed discussion of the intelligence warfighting function. See FM 5-0 for a detailed discussion of military planning and operations.
THE INTELLIGENCE ANALYST
1-3. To effectively execute missions across the full spectrum of military operations, the commander requires intelligence about the enemy and other conditions of the operational environment prior to and during operations. The operational environment is a composite of the conditions, circumstances, and influences that affect the employment of capabilities and bear on the decision of the commander (JP 3-0). The operational environment encompasses physical areas and factors of the air, land, maritime, and space domains. It also includes the information environment and enemy, adversary, friendly, and neutral systems.
1-4. The analyst is directly responsible for aiding the commander’s understanding of how current and potential enemies organize, equip, recruit, train, employ, and control their forces. The analyst also aids the commander’s understanding of the terrain and weather and their effects upon both friendly and enemy operations. This includes the military aspects of the terrain and weather as well as civil considerations.
…