
Phishing is an attempt to acquire information such as usernames, passwords, account numbers, and credit card details by masquerading as a trustworthy entity in an electronic communication.
The report presents the key findings of the Afghanistan Opium Survey 2015. The full report on cultivation and production will be published in November and a separate report with a socioeconomic analysis will be presented early 2016. The survey is implemented annually by MCN in collaboration with the UNODC. The survey team collects and analyses information on the location and extent of opium cultivation, potential opium production and the socio-economic situation in rural areas. Since 2005, MCN and UNODC have also been involved in the verification of opium eradication conducted by provincial governors and poppy-eradication forces. The information is essential for planning, implementing and monitoring the impact of measures required for tackling a problem that has serious implications for Afghanistan and the international community.
This report fulfills the requirement contained in the National Defense Authorization Act (NDAA) for Fiscal Year (FY) 2014, Section 933(e) “National Guard Assessment.” The results of the National Guard’s assessment reflect the Chief of the National Guard Bureau’s (CNGB) view for successfully integrating the National Guard into the Department of Defense’s (DoD) Cyber Mission Force (CMF) and across all Cyber missions to create a Whole of Government and Whole of Nation approach to securing U.S. cyberspace.

This report fulfills the requirement contained in the National Defense Authorization Act (NDAA) for Fiscal Year 2014, Section 933 “Mission Analysis for Cyber Operations of the Department of Defense (DoD).” The Department undertook an accelerated but deliberate process to conduct the analysis, the outcomes of which are contained in this report. The analysis addressed each sub-section of the statute and was fully vetted across the Department. The results of this analysis reflect the Department’s current view of its requirements for successful conduct of cyberspace operations, leveraging a Total Force solution. As cyberspace capabilities, force structure, and command and control (C2) constructs evolve, the Department will conduct periodic reviews of its cyberspace requirements and adjust them as necessary.

Foreign fighters are pouring into Iraq and Syria from all over the world to take up arms with the Islamic State (ISIL). Recent reports have estimated that as many as 30,000 foreign fighters may be fighting in Iraq and Syria and that they are flowing in at a rate of nearly 1,000 new recruits a month. However, a recently emerging phenomenon of Western individuals, primarily veterans, returning to Iraq and Syria to fight against ISIL forces has only recently begun to receive significant media attention. No one has a precise number on how many Westerners are actually fighting in the conflict against ISIL, though estimates often place the number somewhere around 100-130 foreign fighters.

This Joint Intelligence Bulletin highlights the potential risks for US persons traveling to Syria or Iraq to combat the Islamic State of Iraq and the Levant (ISIL) or expressing online a desire to do so. The FBI, DHS, and NCTC remain concerned that US persons traveling to combat ISIL are at risk of being killed, wounded, or captured. Further, ISIL members or supporters could attempt disingenuously to identify and target US persons so as to harm them before or upon their arrival in Syria or Iraq. The State Department has issued travel warnings for both Iraq and Syria and the US Government does not support US persons traveling overseas to combat ISIL.
During FY 2014, the SOCCENT Commander requested a short-term effort to understand the psychological, ideological, narrative, emotional, cultural, and inspirational (“intangible”) nature of ISIL. As shown below, the SMA1 team really addressed two related questions: “What makes ISIL attractive?” or how has the idea or ideology of ISIL gained purchase with different demographics; and “What makes ISIL successful?” or which of the organization’s characteristics and which of the tactics it has employed account for its push across Syria and Iraq. The effort produced both high-level results and detailed analyses of the factors contributing to each question. The central finding was this: While military action might degrade or defeat factors that make ISIL successful, it cannot overcome what makes ISIL’s message and idea attractive.

As of July 2015, an APT actor that has previously targeted the U.S. financial sector used an implant to provide command and control (C2), according to credible reporting. Implant communications were observed between administrative infrastructure and known malware C2 nodes used in spear-phishing campaigns in July 2015. The communication from administrative infrastructure was an HTTP POST request.
The Criminal Justice Information Services (CJIS) Division’s Quick Capture Platform (QCP) is a state-of-the-art biometric system that enables investigators to collect and store fingerprint data during domestic and international investigations. The QCP enables instant access to federal fingerprint databases. This comprehensive access to the main United States (U.S.) Government biometric holdings enables QCP users to quickly establish whether a subject has possible terrorist links (in the U.S. or abroad) or is likely to pose a threat to the U.S.
SWATTING is the act of sending a SWAT team or some type of law enforcement response to a location by convincing law enforcement that an incident has occurred or is about to occur that requires immediate law enforcement response. Characteristics of swatting include, but are not limited to: Callers using internet-based phones such as Skype USBUS and Magic Jack USBUS, or callers using a legal Caller Identification (ID) masking service. Caller ID spoofing/masking services permit cell phones and landline phones to spoof the call’s origins through a service fee based software. Reports of bomb-threats and SWATTING incidents are coming from area elementary, middle, and high schools, along with universities as well. Federal, state, and local partners are working to identify where the calls are originating from.
This publication identifies multi-Service tactics, techniques, and procedures (MTTP) for Defense Support of Civil Authorities (DSCA). At the tactical level, it assists military planners, commanders, and individual Department of Defense (DOD) components employing military resources and integrating with National Guard Civil Support activities while responding to domestic emergencies in accordance with United States (US) law.

Senegal is a diverse West African nation approximately the size of South Dakota and home to more than 36 ethnic groups and languages. Senegal’s national development has been shaped by its location between the edge of the Sahara and the Atlantic. Trans-Saharan trade brought Islam and Arab influences to Senegal through North Africa. Later, Senegal became one of the first African countries to trade with Europe through the Atlantic seaways. Today, Senegal is seen by the Senegalese as a bridge between Black African, Islamic, and European civilizations.
FID is participation by civilian and military agencies of a government in any of the action programs taken by another government or other designated organization to free and protect its society from subversion, lawlessness, insurgency, terrorism, and other threats to its security (Joint Publication [JP] 3-22, Foreign Internal Defense). This publication depicts the integrated theater efforts that include ARSOF and conventional forces roles in joint, multinational, intergovernmental, and nongovernmental organizations working in a collaborative environment. It provides an overview of selected sources of power applied through the instruments of national power brought to bear for supporting FID and the impact and interaction of Army units with the other instruments of national power. In addition, it illustrates how FID is a key component of a host nation’s (HN’s) program of internal defense and development (IDAD), and that the focus of all U.S. FID efforts is to support that IDAD program to build capability and capacity to free and protect the HN from subversion, lawlessness, and insurgency.
Indonesia is a geographic mixing point between the traditional Malay peoples of most of Southeast Asia and the Austronesian peoples to the east. The country’s territory stretches thousands of miles from east to west and has a centuries-old history of settlement and interaction with the region and rest of the world. Consequently its culture and society reflect influences from China, India, the Middle East, and other areas of Southeast Asia.

Kuwaiti Arabs comprise 45 percent (approximately 950,000) of the population in Kuwait. “Arab” is a name originally given to the nomadic inhabitants of the Arabian Peninsula. It is now largely a cultural/linguistic designation, embracing various national, regional, and religious groups in several different countries.

Cryptography has emerged as a powerful tool that can help to assure the confidentiality, non-repudiability and integrity of information in transit and storage as well as to authenticate the asserted identity of individuals and computer systems. Encryption technology was traditionally deployed most widely to protect the confidentiality of military and diplomatic communication. With the advent of computer and Internet revolution and online applications as well as the recent innovations in the science of encryption, a new market for cryptographic products in E-commerce & E-Governance civilian applications has rapidly developed. Communication and E-commerce applications such as electronic mail and electronic fund transfer, which require secure means of communication, make extensive use of encryption for securing the information and authentication.
We are transitioning PGP keys in conjunction with the establishment of new security procedures. We are moving from our old key (0x5FE1B448) to our new key (0xD0516538).

The Philippines Cultural Field Guide is designed to provide deploying military personnel an overview of the Philippines’ cultural terrain. In this field guide, the Philippines’ cultural history has been synopsized to capture the more significant aspects of the Philippine cultural environment, with emphasis on factors having the greatest potential to impact operations.
Morocco’s military traditions are closely linked with the country’s history and are influenced by its extensive political and cultural heritage. Morocco’s history, and thus its military history, began in the Medieval Islamic period, 12 centuries before the end of the French and Spanish protectorate in 1956, which is often represented as the year Morocco became independent. Moroccans, however, consider 1956 the year the country regained its independence after 44 years of foreign rule. Although foreign rule profoundly transformed Morocco’s economy and infrastructure, Moroccans view the post-protectorate period as a reversion to independent rule by the reigning Alawi or Filali dynasties, which had held power in the country since 1660. Mohamed V presided over this independent rule and military modernization for 34 years (1927–1961). Moroccans inherited a modernized state, albeit with surviving traditional institutions, from their former European rulers, and the dynastic continuity under the protectorate ensured the prominent re-emergence of indigenous influence in many areas, including the military.

Prior to sending any request to a foreign country, make sure your have exhausted all internal/national sources of obtaining the required electronic data/evidence. Note that this data/evidence can be obtained, among other things, from open sources (i.e. publicly available information) and/or directly from Internet Service Providers (ISPs) established/registered in your country as affiliate companies of foreign-based ISPs.
Given the complexity and lethality of national security threats in the maritime domain, and in support of the U.S. National Strategy for Maritime Security, and the Sea Services’ (Navy, Marine Corps, and Coast Guard) joint maritime strategy, A Cooperative Strategy for 21st Century Sea Power, it is vital to America’s interests that the Navy and Coast Guard collaboratively plan, field, and sustain interoperable and affordable forces to provide complementary support for each other’s mission sets. As good stewards of the Nation’s resources and faced with an uncertain budget environment, it is imperative that our services cooperate in a deliberate manner. Implementation of the National Fleet Policy will provide the Nation with more interoperable and fiscally efficient Navy and Coast Guard forces. The National Fleet Plan identifies specific Navy and Coast Guard authorities, methods, and measurements to avoid redundancies and achieve economies of scale. It improves operational effectiveness and provides a mechanism to enhance integration and resource development. The Plan is adaptive to meet emerging national security threats and scalable to address changing service challenges.
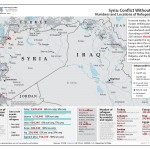
In recent weeks, the upsurge of Syrians seeking asylum in European countries has overwhelmed existing capacity. According to UNHCR, as of July 2015 almost 350,000 Syrians have applied for asylum in Europe since the conflict in Syria began, nearly half applying in Germany and Sweden and one third in Serbia, Hungary, Austria, Bulgaria, and the Netherlands combined.

Moroccan culture uniquely combines aspects of Europe, the Middle East, and Africa. It is a Muslim country with close ties to other Arab countries in the Middle East, but its proximity to Europe has given it a more Western feel. Morocco experiences many of the economic hardships seen in other African nations, such as a lack of economic diversity, high unemployment, and widespread poverty.