Public Intelligence
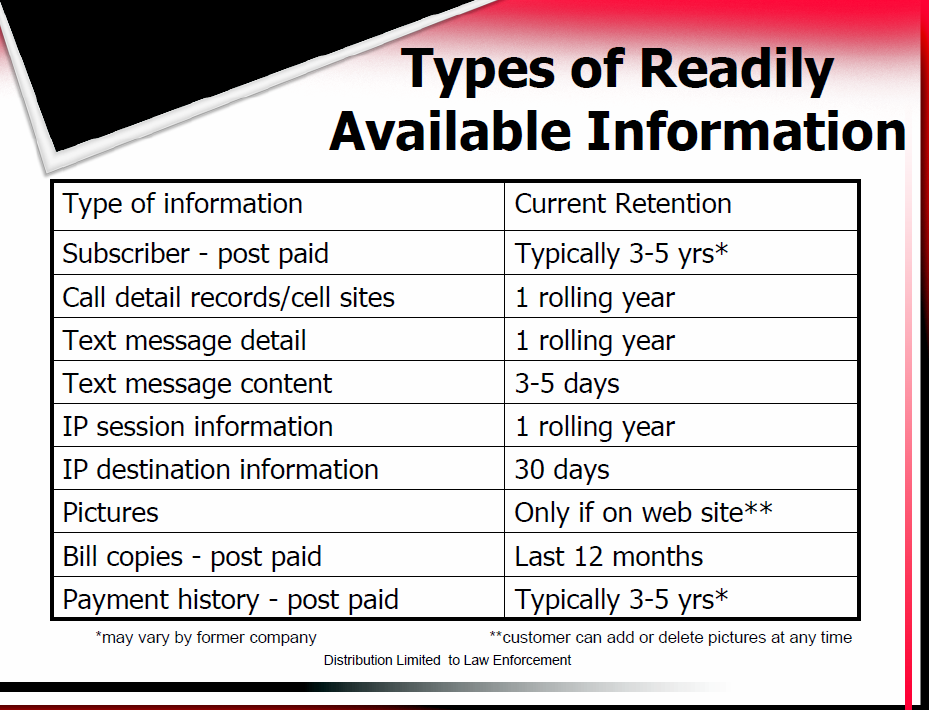
For some time, it has been apparent that wireless telephone providers are storing location data on all of their customers. This information indicates the location of an individual’s cellular phone signal from its corresponding cellular tower to provide an approximate location of the user at any given time. Wireless providers are paid for supplying this information to law enforcement and the companies work to provide user-friendly guides to potential customers indicating what details they can provide.
We have previously published law enforcement subpoena guides from Verizon, Nextel, MetroPCS, T-Mobile, AT&T, Sprint, among other service providers. Many of the companies providing this information to law enforcement take steps to hide the reality of their information retention. One guide in particular, regarding the Verizon Wireless Law Enforcement Resource Team, is labeled as being only distributable among law enforcement personnel. The guide advertises a wide variety of services available to law enforcement, including details on any user’s “cell sites” going back nearly one year. Another subpoena guide produced by Verizon offers a price list for these services including $125 an hour for “expert testimony”. Active surveillance using trap and trace is the most lucrative for Verizon with a price of up to $1000 a month, not including setup fees and other administrative costs.
A new, confidential telephone investigations guide obtained by Public Intelligence indicates that law enforcement officers are encouraged not to inform courts or suspects as to how this sort of information is acquired. A disclaimer at the back of the guide reads: “Do not disclose this information in court anymore than is absolutely necessary to make your case.” The disclaimer goes on to say:
Never disclose to the media these techniques – especially cell tower tracking. Simply state, “Through further investigation we were able to locate the suspect (or missing person)”.
Though information regarding cellphone tracking is widely available and suspects in criminal investigations have been caught utilizing this information, law enforcement personnel evidently do not want people to know that their cellphone is tracking them throughout the day as they make their calls. With the advent of GPS systems and location-based services in cellular phones, this tracking is likely to increase. This new corporate surveillance model, which has grown steadily in recent years, differs from previous models of governmental surveillance in numerous ways. By encouraging corporate service providers to surveil their users and retain complex records regarding their habits, government and law enforcement have created a model whereby surveillance can be both legally legitimate and profitable. Corporations even work to provide government clients with competing services to ease in disseminating this information, as past “spying guides” published by Cryptome demonstrate.
Beyond the potential for abuse, what is most disturbing about these data retention practices is the fact that they are not disclosed in a clear way to consumers. Sometimes corporate practices can be openly deceptive in this regard. For example, we have previously published guides from Microsoft teaching law enforcement personnel how to break encryption systems that are sold to the public as being able to protect data against unwanted intrusion. Likewise, the majority of users of Facebook or MySpace are likely not aware that all of their actions, photographs, and content is being retained along with identifying information in case of a legal request. Such practices effectively skirt the illegality of this invasive and unwarranted surveillance by maintaining the appearance of constitutionality in requiring subpoenas and court orders to deliver data. However, as past examples demonstrate, sometimes this legal prerequisite can be abandoned due to perceived threats to “national security”.
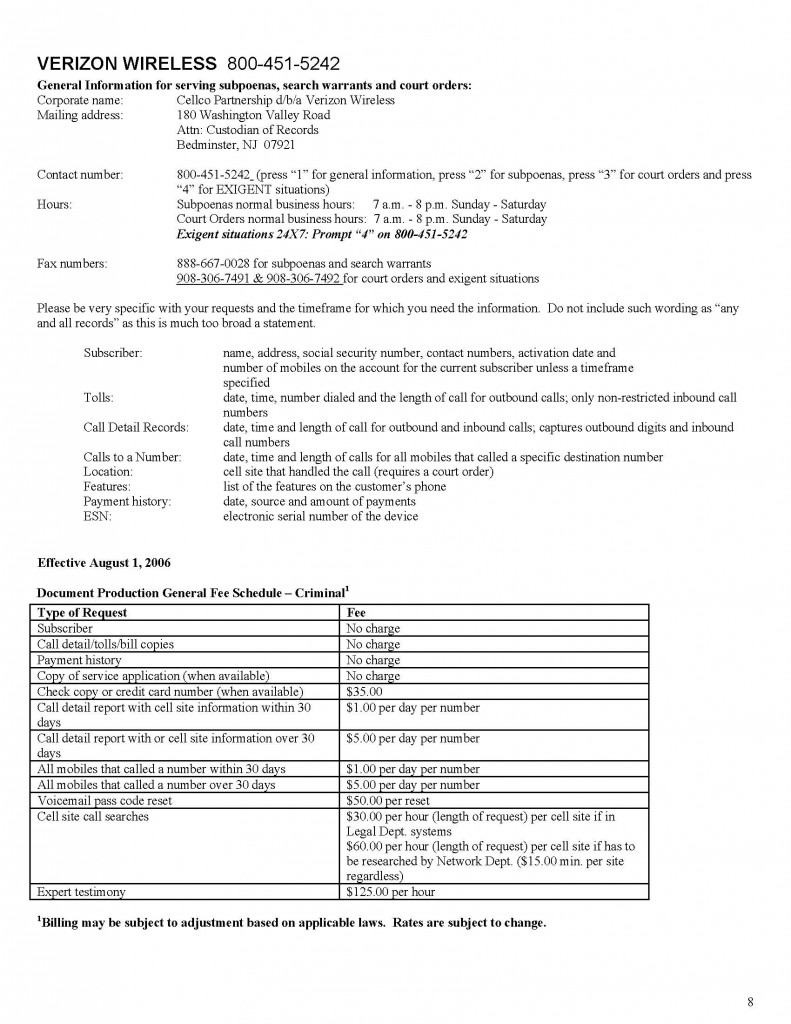
A page from Verizon's Law Enforcement Compliance Guide describing prices for providing various information regarding its customers.