A 2016 presentation on the FBI National Instant Criminal Background Check System (NICS) used for firearms purchases.
This data set consists of twenty-one teleoperated weapons systems used by terrorist and insurgent groups. It is worth noting that there are many more systems’ images available, but no group affiliation could be associated with them, which is why they were not included in this research project. The plethora of videos and photos on social media indicates that terror and insurgent groups are increasingly turning to improvised weaponry use on the battlefield. One class of improvised weapon that is emerging is remote controlled sniper rifles and machine guns. They are being used across Syria, Iraq, and a lone case in Libya as early as 2011. Typically, rifles or machine guns are improvised to be secured on a base—either mobile or stationary—and linked to cables, which are connected to a remote and screen. Some systems are more refined than others, such as with cameras, but all have at least proven to be somewhat effective.
In June 2013, former National Security Agency (NSA) contractor Edward Snowden perpetrated the largest and most damaging public release of classified information in U.S. intelligence history. In August 2014, the Chairman and Ranking Member of the House Permanent Select Committee on Intelligence (HPSCI) directed Committee staff to carry out a comprehensive review of the unauthorized disclosures. The aim of the review was to allow the Committee to explain to other Members of Congress–and, where possible, the American people–how this breach occurred, what the U.S. Government knows about the man who committed it, and whether the security shortfalls it highlighted had been remedied.
The FBI received information of an additional IP address, 5.149.249.172, which was detected in the July 2016 compromise of a state’s Board of Election Web site. Additionally, in August 2016 attempted intrusion activities into another state’s Board of Election system identified the IP address, 185.104.9.39 used in the aforementioned compromise.
The purpose of this LIR is to inform DSAC and other relevant private sector partners about new methods ATM skimming crews use to target standalone or kiosk-style ATM terminals such as those found at casinos, hotels, airports, shopping malls, gas stations, restaurants, and supermarkets. The skimming crews intercept customers’ account data through the ATMs’ external cables. The activity observed to date in the United States was discovered at convenience store locations in California, Delaware, and Pennsylvania. This LIR provides details on the methods used in these skimming attempts as well as previously reported use of internal wiretap skimming devices.

The healthcare sector has been a desirable target for hackers due to the sensitive nature of patient information contained in their systems. The stakes are very high in the healthcare industry because any disruption in operations and care can have significant repercussions for patients. As such, this industry offers an ideal victim for ransomware, and these attacks are likely to continue—disrupting employee access to important documents and patient data and hampering the ability to provide critical services—creating a public safety concern.
On July 10, 2015, the Federal Bureau of Investigation (FBI) initiated a full investigation based upon a referral received from the US Intelligence Community Inspector General (ICIG), submitted in accordance with Section 811 (c) of the Intelligence Authorization Act of 1995 and dated July 6, 2015, regarding the potential unauthorized transmission and storage of classified information on the personal e-mail server of former Secretary of State Hillary Clinton (Clinton). The FBI’s investigation focused on determining whether classified information was transmitted or stored on unclassified systems in violation of federal criminal statutes and whether classified information was compromised by unauthorized individuals, to include foreign governments or intelligence services, via cyber intrusion or other means.

EXIF (Exchangeable image File Format) is a standard format for storing and exchanging image metadata. Image metadata is included in a captured image file and provides a broad range of supplemental information. Some social networks and photo-sharing sites, such as Flickr, Google+, and Instagram, have features that share EXIF data alongside images. Others, including Facebook and Twitter, do not share EXIF data but my utilize the information internally. EXIF data is stored as tags, some of which reveal unique identifying information.

LinkedIn is a professional networking service that allows you to establish connections with co-workers, customers, business contacts, and potential employees and employers. You can post and share information about current and previous employment, education, military activities, specialties, and interests. To limit exposure of your personal information, you can manage who can view your profile and activities.

Anonymous email services can be used to send personal or work-related messages without leaving a trace of your identity. Truly anonymous email accounts require no personal information to register and retain little usage data. Anonymous email accounts should always be accessed and used in conjunction with an anonymous IP address.
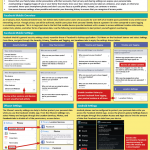
As of January 2015, Facebook Mobile hosts 745 million daily mobile active users who accounts for over 60% of all mobile posts published to any online social networking service. Though privacy can still be achieved, mobile users place their personal identity data at a greater risk when compared to users logging in via desktop computer. This is in large part due to the fact that mobile devices provide Facebook with a means to access additional location information, contact lists, photos, and other forms of personal data. Use the following recommendations to best protect yourself against oversharing.

Facebook provides shortcuts to their privacy settings that help to limit what others can see in your profile. Select Privacy Checkup to change your basic privacy settings. For more extensive settings, click See More Settings. From there, navigate through the pages of the settings toolbar to control how your personal information is shared with others.

To locate your presence on the web, search for your name, names of family members, email addresses, phone numbers, home addresses, and social media usernames using Google. Once you have located information that you want removed, record your findings to keep track of the removal process. Please note that the information presented here about how to remove personal details from data aggregators is subject to change.
This training circular provides GEOINT guidance for commanders, staffs, trainers, engineers, and military intelligence personnel at all echelons. It forms the foundation for GEOINT doctrine development. It also serves as a reference for personnel who are developing doctrine; tactics, techniques, and procedures; materiel and force structure; and institutional and unit training for intelligence operations.
Russia’s strategic objectives in the Baltic region do not focus on the Baltic States as final targets, but on using the Batlic States to discredit and dismantle the North Atlantic Treaty Organization (NATO) and undermining the European Union (EU) by using the Baltic States. Experts in Russia and European security from the United States and the Baltic region agree that Russia could use the Baltic States toward this end by employing any one of a spectrum of actions, to include direct invasion with conventional forces, an incursion and occupation using irregular forces like the one witnessed in Crimea in 2014, or longterm fostering of social, political, and economic instability. Disagreement existed among experts as to which approach was more likely.
This manual is composed of several volumes, each containing its own purpose. In accordance with the authority in DoD Directives (DoDDs) 5111.13 and 3025.18 the manual assigns responsibilities and establishes procedures for Defense Support of Civil Authorities (DSCA) and identifies authorities for DoD Components to provide support of civil authorities and non-DoD entities. For DoD support described in this manual that is not under the oversight of the Assistant Secretary of Defense for Homeland Defense and Global Security (ASD(HD&GS)), this manual identifies the offices of responsibility and oversight.
What follows is an assessment of the Islamic State of Iraq and the Levant (ISIL) from a socio-cultural perspective. We have employed a modified PMESII-PT framework for analysis (Political, Military, Economic, Social, Infrastructure, Information, Physical Terrain, Time). We have modified PMESII-PT in three ways to emphasize the socio-cultural aspect of this analysis. First, we have expanded the concept of Military to cover all coercive forces in the area of interest. The expanded category includes law enforcement, pro and anti-government paramilitaries, militias, external forces, etc. Second, we added Population and Culture as separate categories. Arguably, these categories could be covered in PMESII-PT under Society, but we saw them as sufficiently important to merit separate chapters. Third, we have expanded the concept of Information, which we have titled Communications, to account for both how information is communicated and how it is received within the society under analysis. With that as background, here is a synopsis of our major findings by category in our modified PMESII-PT framework.
The Joint Task Force was created by the Chairmen of the House Armed Services Committee, the House Permanent Select Committee on Intelligence, and the House Appropriations Subcommittee on Defense to investigate the allegations of a whistleblower that intelligence produced by U.S. Central Command (CENTCOM) had been manipulated to present an unduly positive outlook on CENTCOM efforts to train the Iraqi Security Forces (ISF) and combat the self-proclaimed Islamic State of Iraq and the Levant (ISIL). Although investigations into the whistleblower’s allegations continue, the Joint Task Force has conducted sufficient investigation to reach certain interim conclusions. Those conclusions are contained in this report. However, the Joint Task Force awaits the completion of the ongoing Department of Defense Inspector General (DODIG) investigation into this matter.

Chinese Talent Programs are a vital part of Chinese industry. Talent programs recruit experts to fill technical jobs that drive innovation and growth in China’s economy. National, provincial, and municipal talent recruitment programs provide opportunities for experts to work in industry and academic organizations supporting key areas deemed critical to China’s development. The talent programs recruit experts globally from businesses, industry, and universities with multiple incentives to work in China. Associating with these talent programs is legal and breaks no laws; however, individuals who agree to the Chinese terms must understand what is and is not legal under US law when sharing information. A simple download of intellectual property (IP) or proprietary information has the potential to become criminal activity.