The 16 April 2013 sabotage of optic cables and electricity transformers supplying Silicon Valley highlighted the vulnerability of critical infrastructure to deliberate, malicious harm.
This document identifies recommended actions and guidance for state and major urban area fusion centers (fusion centers) to integrate information technology, cybersecurity, and cybercrime1 prevention (cyber) intelligence and analytic capabilities. Development of these capabilities will inform local, state, and national detection, mitigation, response, recovery, investigation, and criminal prosecution activities that support and maintain the United States’ cybersecurity.
The vision of the 2014–2017 National Strategy is to connect the geographic and public safety diversity of over 38,000 states, counties, cities, and towns together in a way that creates a national information sharing asset that is coordinated with and contributes to federal information sharing efforts. Federal efforts to connect the knowledge and capabilities of the Intelligence Community (IC) often involve state and local law enforcement joining federal efforts. The NNFC is the reversal and broadening of this framework, inviting federal partners to join state and local public safety information sharing efforts. In carrying out this strategy, IC professionals have an opportunity and avenue to bring their knowledge and capabilities to state and major urban area fusion centers, designated by governors and staffed by state and local professionals. As a unique national asset, this state and local network must work seamlessly with field-based intelligence and information sharing entities, providing geographic and interdisciplinary knowledge and perspective without interrupting or replicating federal efforts. The 2014–2017 National Strategy integrates with other criminal intelligence sharing efforts supported by the Criminal Intelligence Coordinating Council.
The Virginia Fusion Center (VFC) has observed via open sources that actors affiliated with the Anonymous hacktivist movement released a video which purportedly identifies a Chicago Office of Emergency Management and Communications (OEMC) vehicle as a tool for law enforcement wiretapping efforts by police and fusion center personnel in Chicago, Illinois. The VFC is sharing this information for situational awareness, as emergency management vehicles operating near protest areas may be targeted by precipitating violent or malicious activity.
The Colorado Information Analysis Center (CIAC) is disseminating this awareness bulletin to help law enforcement officers and military personnel to minimize their social media footprint and protect their identity and family. Recent calls for attacks against law enforcement officers by foreign terrorist organizations and recent reports released by the U.S. Senate Select Intelligence Committee’s report on the CIA’s Detention Interrogation Program may exacerbate tensions or even spark violence against officers, intelligence personnel, government officials, and their families. This awareness bulletin seeks to make general recommendations to limit an individual’s digital footprint and diminish a violent actor’s targeting capability.
Propaganda providing guidance and/or encouraging “individual jihad” or small cell operations against the West continues to be a prevalent theme in jihadist messaging. This bulletin was created by the CFIX in order to address recent propaganda from the Islamic State and its supporters which provides guidance on targeting law enforcement officers. The CFIX bases its analysis in this bulletin from open source reporting and internet postings with varying degrees of reliability, especially in regards to the true intention and capabilities of terrorist organizations and their supporters. This information is intended to support local, state and federal government agencies along with other entities in developing / prioritizing protective and support measures relating to an existing or emerging threat to homeland security.
The purpose of this brief is to provide law enforcement, first responders, corrections officers, and other personnel who interact with the general public, with guidance and protective measures when coming in contact with individuals demonstrating symptoms of the Ebola Virus Disease (EVD). Personnel who become familiar with the identification of possible exposure, proper response protocols and protective measures will be better prepared to respond, secure, transport and decontaminate to prevent further spread of this deadly disease.
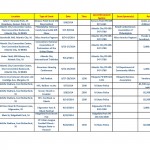
The NJ Office of Homeland Security and Preparedness (OHSP) compiles a statewide list of special events that provides situational awareness to law enforcement, as well as to assist in local planning requirements. Special events include any event that attracts large numbers of participants and spectators in both a public or private venue. Examples include concerts, marathons, firework displays, community celebrations, visits by VIPs, sporting events, holiday gatherings, etc.
The expansion of Unmanned Aerial Vehicle (UAV) operations for military purposes in the last decade has driven growth in the commercial UAV industry where. the casual enthusiast can now purchase a ready-to-fly system for less than $300. These UAVs can be accessorized for varied purposes such as cinematography, agricultural monitoring, wildlife tracking, site surveillance, and potentially even for kinetic attacks with a firearm or improvised explosive. This Advisory Bulletin addresses an observed increase in UAV use by ordinary citizens, outlining capabilities and implications for the law enforcement community. The NCRIC has not received any specific or credible UAV threats in our 15-county AOR and presents the following information for situational awareness purposes.

The FBI San Antonio Division recently reported that groups of young individuals in Texas, and possibly other states, were attempting to elicit information regarding residences of firefighters, military personnel, police officers, etc. The subjects knocked on neighborhood doors, telling residents they worked for an organization that helps young people with public speaking by sending them out to contact random people at their homes and ask about their professions. The youths reportedly received points based on the professions they located, with the potential of winning a college scholarship and a large sum of money. Police officer had the highest point value.
Humming bird and Marilyn Monroe tattoos may have a nexus to the Mexican Mafia, while “G Shields” (Aztec warrior shields) and mariposas (butterflies) may be decreasing in popularity. As certain tattoos sported by Mexican Mafia members and supporters become mainstream, and because California Department of Corrections is known to use certain tattoos as validation points, Mexican Mafia members may introduce new tattoos to make it difficult for law enforcement and correctional officers to identify membership or affiliation with the group. Tattoos are also increasingly disguised within other tattoos, which can make them more difficult to easily identify.
First responders, such as law enforcement, emergency medical services (EMS), and firefighters, often arrive at incidents completely focused on the emergency at hand. Whether it is a fire, a chest pain complaint, or a vehicular accident, the first responders prepare for certain events to take place during emergency situations and personal safety is a priority throughout the response. Unfortunately, in the past few years there are have been several occurrences where first responders became the victims of ambushes while performing their duties to protect citizens and save lives.

Over the last week there have been three attacks – one in Canada and two in the United States – in which law enforcement officers were targeted, leading to the death of five officers and one civilian. Based upon reporting it appears all the suspects in these incidents were motivated by elements of a far right anti-government ideology with a particular fixation on law enforcement. While it is unknown whether this spike is indicative of a long term increasing trend, it is significant from a near term perspective due to the short time frame and purposeful targeting of law enforcement.

Incidents involving the theft of fuel (gasoline, diesel, kerosene, ethanol, etc.) from fuel storage tanks have been reported across the United States. Fuel theft has significant health and safety implications, including risk for spills, fires, and explosions. Fuel thieves typically do not adhere to security standards or practices, and may inadvertently expose fuel to a hot engine, lit cigarette, or ignition source. First responders and other maintenance personnel also may be exposed to fuels through skin contact or inhalation routes during recovery and/or cleanup operations, which can result in potential health effects.

The Knox-Box® rapid entry system is an access control system utilized by public safety agencies. This system allows facilities to securely store entry keys or cards on site for first responders. First responders utilize a master key that unlocks all Knox boxes within their jurisdiction. Currently there are over 3.5 million Knox-Box rapid entry systems in use nationwide and over 11,500 fire departments in North America that use the Knox-Box rapid entry system. In one Colorado fire district there are over 4,000 Knox-Box systems in use within the local, state, and federal government which includes; energy, water, postal, emergency services, defense, transportation, and communication sectors. Unauthorized access to the system would allow individuals to bypass physical security measures at the site. The unauthorized individuals would also be able to duplicate keys, or remove entry keys or cards which would delay first responders.

The State of Colorado legalized medical marijuana in 2012 and recreational marijuana in 2014. There has been an increased amount of marijuana infused products sold to the public. The products range from fruit chewz, gummiez, cupcakes, truffles, rice krispy treats, butter, and banana bread. It is extremely difficult to differentiate between marijuana infused products and non-infused products if the original packaging is not with the product.

In the past year, the NJ Suspicious Activity Reporting System (NJ SARS) has received multiple reports of intrusions at electrical grid facilities in New Jersey. The NJ ROIC currently has no indication of any specific threats associated with these incidents, but provides this information for situational awareness and requests information on any similar, previously unreported incidents in New Jersey.
In December 2012 the President signed the National Strategy for Information Sharing and Safeguarding (Strategy) which is anchored on the 2010 National Security Strategy and builds upon the 2007 National Strategy for Information Sharing. The Strategy provides guidance for more effective integration and implementation of policies, processes, standards, and technologies to promote secure and responsible national security information sharing. This document provides a higher-level overview of a longer, more detailed implementation plan for the Strategy, and is intended to assist in briefing senior policy makers on plans, progress, and performance related to achieving the vision of the NSISS.
On Saturday, September 21, 2013, members of Al Shabaab, a Somali based Islamic terrorist organization affiliated with the international Al Qaeda network, executed a complex terrorist attack on an upscale shopping mall in Nairobi, Kenya. The attackers simultaneously entered the mall from two different entrances, shooting shoppers with assault rifles and throwing hand grenades. The terrorists remained in the mall, engaging government security forces for the next four days, resulting in a major fire and partial collapse of the mall. The Kenyan government has officially reported 72 deaths and more than 200 injured as a result of the attack. A significant number of those killed and injured were foreign citizens, including 6 U.S. citizens who were injured in the attack.
The purpose of this bulletin is to provide awareness and a basic understanding of the “Hidden Internet” to investigators in the field, as well as provide some examples of how the Hidden Internet can be exploited by criminal elements. While the term “Hidden Internet” can be used in a broader context and refer to other internet terms such as the “Deep Web” or “Deepnet,” for the purpose of this bulletin the term “Hidden Internet” will refer to the hidden services provided by the TOR project to internet users, specifically relating to the Silk road website and use of Bitcoins.

A collection of hundreds of emails from the City of Oakland relating to the construction of the City/Port of Oakland Joint Domain Awareness Center. The files were obtained through a public records request made by members of Occupy Oakland. The emails range in date from September 2013 to December 2013.