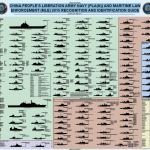
A poster depicting various vessels in the Chinese People’s Liberation Army Navy (PLA(N)) and Maritime Law Enforcement (MLE) that was produced by the Office of Naval Intelligence and is current as of February 2015.
Today, Strategic Landpower faces a complex and interconnected global operational environment characterized by a multitude of actors with unknown identities. This presents a wider range of possible threats than encountered before. Our operational environment has fewer well-defined friends and foes with most actors presented along a continuum of: unknown to partially known to known, throughout the range of military operations. Many found in the middle are susceptible to persuasion. Each of these actors has an agenda, often at odds with our objectives, those of other actors, and the goals of the existing political order. Besides a broad range of readily available conventional weapons, state and non-state actors can select from an array of affordable technologies, adapting them to create unexpected and lethal weapons. Social media enables even small groups to mobilize people and resources in ways that can quickly constrain or disrupt operations. This complex operating environment continuously evolves as conditions change and test our ability to innovate and adapt. The complexity reconfirms the imperative to understand, plan, and employ Identity processes and capabilities within land operations.
This is the first unclassified Australian Cyber Security Centre (ACSC) Threat Report. All ACSC partner agencies have contributed to provide information tailored for Australian organisations about the threats their networks face from cyber espionage, cyber attacks and cybercrime. It also contains mitigation and remediation information to assist organisations to prevent, and respond to, the threat.
Militia extremists are expanding their target sets to include Muslims and Islamic religious institutions in the United States. This has resulted in increased violent rhetoric and plotting and has the potential to lead, over the long term, to additional harassment of or violence against Muslims by domestic extremists. The FBI makes these assessments with high confidence on the basis of a large body of source reporting generated mainly since 2013. This information augments prior FBI analysis that established militia extremists target government personnel and law enforcement officers, perceived threats from abroad, and individuals or institutions that seek to constrain Second Amendment rights.
This report looks in greater depth at the phenomenon of global jihadism and how it manifests itself in the Netherlands. It addresses the question of what global jihadism actually involves and what factors have led to its current revival. We must try to understand jihadism and the form it takes in the Netherlands: an understanding of this phenomenon, and of its underlying processes and motives, is a vital prerequisite for devising an appropriate approach. This analysis therefore starts with the ideology behind jihadism. It will also reflect on the process of radicalisation that occurs before a person embraces extremist views. After all, in order to intervene effectively to halt radicalisation it is important to understand the potential appeal of extremist ideas and why some people are susceptible to them.
Upon request by the LIBE Committee, this study focuses on the question of how to best prevent youth radicalisation in the EU. It evaluates counter-radicalisation policies, both in terms of their efficiency and their broader social and political impact. Building on a conception of radicalisation as a process of escalation, it highlights the need to take into account the relation between individuals, groups and state responses. In this light, it forefronts some of the shortcomings of current policies, such as the difficulties of reporting individuals on the grounds of uncertain assessments of danger and the problem of attributing political grievances to ethnic and religious specificities. Finally, the study highlights the ambiguous nature of pro-active administrative practices and exceptional counter-terrorism legislation and their potentially damaging effects in terms of fundamental rights.
NWP 2-01 is a comprehensive reference detailing the intelligence support available to the naval commander in the successful planning and execution of operations. NWP 2-01 is by nature a refresher and ready resource for the Information Dominance Corps (IDC) intelligence professionals, information warfare officers, and cryptologic technicians; however, the target audience is the operational commander. The publication’s length and content are specifically tailored to ensure a practical and valuable reference for the operational decision maker. NWP 2-01 is the foundation for a series of proposed follow-on Navy tactics, techniques, and procedures (NTTP) publications.
This navy warfare publication describes the nature, forces, organization, and employment of naval special warfare (NSW). Naval special warfare is a relatively small, maritime special operations force (SOF) consisting of approximately 9,250 personnel: 2,700 sea-air-land commandos (SEALS), 700 special warfare combatant-craft crewmen (SWCCs), 750 Reservists, 4,000 combat support (CS) and combat service support (CSS) personnel, and more than 1,100 civilians. NSW constitutes 11 percent of special operations forces and less than 2 percent of United States Navy (USN) forces. NSW costs 3/10ths of one cent (0.3 percent) of every United States (U.S.) defense dollar.

In May 2015, the wife of a US military member was approached in front of her home by two Middle-Eastern males. The men stated that she was the wife of a US interrogator. When she denied their claims, the men laughed. The two men left the area in a dark-colored, four-door sedan with two other Middle-Eastern males in the vehicle. The woman had observed the vehicle in the neighborhood on previous occasions.
A set of training presentations created by the Missouri National Guard through its State Partnership Program with the the Republic of Panama. The presentations include training on the use of multiple tools for analyzing information obtained through electronic surveillance including Pen-Link and i2 Analyst’s Notebook.
A bulletin issued by the FBI Cyber Division discusses a spearphishing campaign targeting U.S. government agencies in June and July of 2015. The campaign utilized a Adobe Flash exploit CVE-2015-5119 that was discovered in the 400GB data archive from hacked Italian surveillance technology company Hacking Team that was released publicly earlier this month. The exploit was being sold as a product of Hacking Team and was listed in their product knowledge base. The bulletin notes that the Flash exploit was being used in phishing emails in June 2015 despite the fact that the Hacking Team data was only made public on July 5, 2015.

The Central Intelligence Agency (CIA) and Department of Homeland Security Office of Intelligence and Analysis (I&A) have both responded to recent requests under the Freedom of Information Act (FOIA) for all records “related to or mentioning the website Public Intelligence” with a glomar response, refusing to admit the existence or nonexistence of records related to the request.

Recent FBI investigations and open source reporting reveal that extortion campaigns conducted via e-mails threatening Distributed Denial of Service (DDoS) attacks continue to expand targets from unregulated activities, such as illegal gaming activity, to now include legitimate business operations. The increase in scope has resulted in additional attacks with Bitcoin ransom amounts trending upwards as well.
In recent years, the growing number and sophistication of threats to the nation’s cyber infrastructure have motivated governors to consider adding or expanding cybersecurity capabilities within state fusion centers. Through fusion centers, states receive classified and unclassified information and intelligence from multiple sources across the nation and combine or “fuse” that information into “products” (for example, law enforcement notices and warnings) that help improve state and national readiness to respond to an attack or threat. Since their inception, fusion centers have become more sophisticated, uniform, and nationally networked. As they have matured and evolved, so have their missions. Originally designed to focus on terrorism, they now address a wider array of threats and hazards, including “accidents; technological events; natural disasters; warfare; and chemical, biological (including pandemic influenza), radiological, nuclear, or explosive events.”

In the first half of 2015 there were at least two instances of Islamic State of Iraq and the Levant (ISIL) inspired individuals in the West expressing interest in targeting law enforcement (LE) to obtain weapons and other specialized gear through theft. As ISIL continues to exhort its individuals in the West to carry out attacks, the potential exists that some terrorists may use this tactic and attempt to steal weapons or issued items, such as credentials, badges, uniforms, radios, ballistic vests, vehicles, and other equipment, which could be used in furtherance of an attack. We note that laws governing the purchase of firearms differ widely among Western nations making this tactic more likely to occur in countries where laws are most restrictive and firearms are harder to obtain through legitimate means.

In November 2014, the Board of Directors of the American Psychological Association engaged our Firm to conduct an independent review of allegations that had been made regarding APA’s issuance of ethical guidelines in 2002 and 2005, and related actions. These ethical guidelines determined whether and under what circumstances psychologists who were APA members could ethically participate in national security interrogations. The gist of the allegations was that APA made these ethics policy decisions as a substantial result of influence from and close relationships with the U.S. Department of Defense (DoD), the Central Intelligence Agency (CIA), and other government entities, which purportedly wanted permissive ethical guidelines so that their psychologists could continue to participate in harsh and abusive interrogation techniques being used by these agencies after the September 11 attacks on the United States. Critics pointed to alleged procedural irregularities and suspicious outcomes regarding APA’s ethics policy decisions and said they resulted from this improper coordination, collaboration, or collusion. Some said APA’s decisions were intentionally made to assist the government in engaging in these “enhanced interrogation techniques.” Some said they were intentionally made to help the government commit torture.

This handbook provides basic reference information on Brazil, including its geography, history, government, military forces, and communications and transportation networks. This information is intended to familiarize military personnel with local customs and area knowledge to assist them during their assignment to Brazil.

This handbook provides basic reference information on Paraguay, including its geography, history, government, military forces, and communications and transportation networks. This information is intended to familiarize military personnel with local customs and area knowledge to assist them during their assignment to Paraguay.

Online radicalization to violence is the process by which an individual is introduced to an ideological message and belief system that encourages movement from mainstream beliefs toward extreme views, primarily through the use of online media, including social networks such as Facebook, Twitter, and YouTube. A result of radical interpretations of mainstream religious or political doctrines, these extreme views tend to justify, promote, incite, or support violence to achieve any number of social, religious, or political changes.

On 23 July 2014, the Human Rights Council, by resolution S-21/1, decided to urgently dispatch an independent, international commission of inquiry to investigate all violations of international humanitarian law and international human rights law in the Occupied Palestinian Territory, including East Jerusalem, particularly in the occupied Gaza Strip, in the context of the military operations conducted since 13 June 2014, whether before, during or after. Pursuant to resolution S-21/1, the President of the Council appointed three experts to the commission: William Schabas (Chair), Mary McGowan Davis and Doudou Diène.

The FBI has obtained information regarding cyber actors who have compromised and stolen sensitive business information and Personally Identifiable Information (PII). Information obtained from victims indicates that PII was a priority target. The FBI notes that stolen PII has been used in other instances to target or otherwise facilitate various malicious activities such as financial fraud though the FBI is not aware of such activity by these groups. Any activity related to these groups detected on a network should be considered an indication of a compromise requiring extensive mitigation and contact with law enforcement.