A recent narcotics investigation led to the arrest of two subjects after they were found to be in possession of sixty (60) pounds of marijuana. During the investigation Agents observed the male subject repeatedly holding a wristwatch to his ear and later found the item to be a cellular phone. A Cellebrite extraction was conducted on this phone which was found to have two SIM cards. Dual SIM cards enable the user to combine different numbers, plans or network carriers. This particular cell phone had one SIM card from A T & T, and the other one from Telcel, New Mexico’s largest mobile phone carrier. An internet search revealed you can purchase these wristwatch cell phones starting at $50.00. There were no markings to identify the brand or carrier of this phone. Law Enforcement is advised to be on the look out for these communication devices when you are in contact with subjects of criminal investigations.
134 search results for "cell phone"
Department of State
U.S. State Department OSAC Cell Phone Video Surveillance Warning
On December 15, 2009, the City of London Police released film footage of hostile reconnaissance conducted in July 2008 by an Algerian national (Subject 1). Subject 1 was stopped by two alert police officers who saw him using his cell phone camera to record video inside Liverpool Street Station in London. When the police officers examined the footage they found 90 minutes of video recording of various sites in and around London and several UK cities to include Tube and mainline rail stations, shopping areas, bars, and restaurants. His detention and the follow-up investigation led to the arrest of Subject 1’s brother (Subject 2) and a third Algerian male (Subject 3). British authorities also looked at 30 other individuals and recovered extremist material supporting al-Qa’ida in the Islamic Maghreb in one residence. Police believe the two brothers may have been fundraising and conducting surveillance for a future terrorist operation.
Germany
German Federal Police Forensic Analysis of Cell Phones and SIM Cards
Bundeskriminalamt German Federal Police Forensic Analysis of Cell Phones and SIM Cards, 2008.
Corporate
Carrier IQ Cellular Phone Intelligence Software Training Materials
A presentation included in a collection of materials related to Trevor Eckhart’s research into the “mobile service intelligence” software produced by Carrier IQ. The document was specifically mentioned in a cease and desist order that the company sent to Eckhart demanding that he remove their “confidential training materials” and take down his analysis of the company’s software. Though the company later withdrew the legal complaint, this presentation remains unavailable from its original location and is only available via a number of mirrors at file-hosting sites.
News
Your Cellphone is Tracking You
For some time, it has been apparent that wireless telephone providers are storing location data on all of their customers. This information indicates the location of an individual’s cellular phone signal from its corresponding cellular tower to provide an approximate location of the user at any given time. Wireless providers are paid for supplying this information to law enforcement and the companies work to provide user-friendly guides to potential customers indicating what details they can provide. We have previously published law enforcement subpoena guides from Verizon, Nextel, MetroPCS, T-Mobile, AT&T, Sprint, among other service providers. Many of the companies providing this information to law enforcement take steps to hide the reality of their information retention. One guide in particular, regarding the Verizon Wireless Law Enforcement Resource Team, is labeled as being only distributable among law enforcement personnel. The guide advertises a wide variety of services available to law enforcement, including details on any user’s “cell sites” going back nearly one year. Another subpoena guide produced by Verizon offers a price list for these services including $125 an hour for “expert testimony”. Active surveillance using trap and trace is the most lucrative for Verizon with a price of up to $1000 a month, not including setup fees and other administrative costs.
Corporate, Department of Justice
Confidential Law Enforcement Telephone, Cellular, Satellite & VoIP Investigation Guide
Confidential Law Enforcement Telephone, Cellular, Satellite & VoIP Investigation Guide, March 10, 2010.
United States
House Oversight Committee Report on Law Enforcement Use of Cell-Site Simulation Technologies

Advances in emerging surveillance technologies like cell-site simulators – devices which transform a cell phone into a real-time tracking device – require careful evaluation to ensure their use is consistent with the protections afforded under the First and Fourth Amendments to the U.S. Constitution. The United States’ military and intelligence agencies have developed robust and sophisticated surveillance technologies for deployment in defense against threats from foreign actors. These technologies are essential to keeping America safe. Increasingly though, domestic law enforcement at the federal, state, and local levels are using surveillance technologies in their every-day crime-fighting activities. In the case of cell-site simulators, this technology is being used to investigate a wide range of criminal activity, from human trafficking to narcotics trafficking, as well as kidnapping, and to assist in the apprehension of dangerous and violent fugitives.
Department of Justice
Department of Justice Policy Guidance: Use of Cell-Site Simulator Technology

Cell-site simulator technology provides valuable assistance in support of important public safety objectives. Whether deployed as part of a fugitive apprehension effort, a complex narcotics investigation, or to locate or rescue a kidnapped child, cell-site simulators fulfill critical operational needs. As with any law enforcement capability, the Department must use cell-site simulators in a manner that is consistent with the requirements and protections of the Constitution, including the Fourth Amendment, and applicable statutory authorities, including the Pen Register Statute. Moreover, any information resulting from the use of cell-site simulators must be handled in a way that is consistent with the array of applicable statutes, regulations, and policies that guide law enforcement in how it may and may not collect, retain, and disclose data.
Intelligence Fusion Centers, New Jersey
(U//FOUO) New Jersey Fusion Center Phone Kidnapping Scams Report
During recent weeks, various sources in law enforcement and media outlets have been reporting phone kidnapping scams occurring in Central and Northern New Jersey and New York. In most incidents, scammers have alleged that a member of the phone scam victim’s family had been involved in a car accident and claimed to have taken the victim’s family member hostage. The scammers then claim they will drop their hostage at a hospital after a certain amount of money (usually $1500‐2000) is wired via Western Union to the scammers, as restitution for damage to the scammer’s vehicle. In addition, the scammers state that they have the hostage’s cell phone and any attempts to call the cell phone or disengage from the conversation will result in the murder or beating of the hostage.
Department of Justice
U.S. Department of Justice Cellular Service Provider Data Retention Guide
U.S. Department of Justice cellular service provider data retention guide originally obtained by American Civil Liberties Union of North Carolina.
Colorado, Intelligence Fusion Centers
(U//FOUO) Colorado Information Analysis Center Smartphone Security Bulletin
Smartphones feature an diverse array of computer capabilities which expose them to many of the vulnerabilities previously confined to computers. These threats have evolved from targeting personal computers (PCs) to hitting smartphones much quicker than some security experts anticipated. It took almost fifteen years for these types of attacks to evolve for PCs, but these attacks have been adapted for smartphones much more quickly. The malicious software (malware) currently targeting smartphones attempts to gather personal information stored on the phone and sell it. Since users often store more of this type of information on smartphones than PCs, in some cases it has become more profitable for hackers to create malware for smartphones than PCs.
Japan, Open Source Center
Open Source Center Japan’s Advanced Mobile Phone Environment
Widespread advanced use of mobile phones in Japan has not come about serendipitously: the Japanese have taken to their cell phones because of the country’s highly advanced mobile phone technology and network infrastructure. Additionally, the government’s ambitious strategic plan to make Japan the most advanced “e-nation” in the world has boosted the industry, created an ideal environment for promoting mobile phone usage beyond simple person-toperson calling, and spurred domestic demand for high-tech handsets.
Bilderberg
Excellent Photos of Participants Leaving 2010 Bilderberg Meeting
The following photos were taken by Quierosaber at the entrance to the Dolce Hotels and Resort in Sitges, Spain during the end of 2010 Bilderberg Meeting. To view the entire set click here.
U.S. Joint Forces Command
Multinational Capability Development Campaign Military Strategic Communication Handbook Draft
Cell phones, smart phones, the Internet, and GPS are increasingly available and are changing the nature of conflict, even in remote areas. Information can now reach out in new ways to global audiences because of the revolution in Information Technology (IT), particularly using cell phones and smart phones. The revival of hybrid warfare manifested in recent developments in the international security environment – such as the Arab Spring, the Ukrainian crisis, the rise of Jihadist-Salafist terrorism, and the European migrant crisis – demonstrates the power of communication, broadly based on IT advantages: messages and perceptions become predominant of physical engagements and strongly impact the behaviour of people. Orchestrated activities carry messages and have a crucial effect on 55 public opinions, decision-making processes, and domestic support.
Intelligence Fusion Centers, Ohio
(U//FOUO) Ohio Fusion Center Network: Swatting Incidents at Schools
SWATTING is the act of sending a SWAT team or some type of law enforcement response to a location by convincing law enforcement that an incident has occurred or is about to occur that requires immediate law enforcement response. Characteristics of swatting include, but are not limited to: Callers using internet-based phones such as Skype USBUS and Magic Jack USBUS, or callers using a legal Caller Identification (ID) masking service. Caller ID spoofing/masking services permit cell phones and landline phones to spoof the call’s origins through a service fee based software. Reports of bomb-threats and SWATTING incidents are coming from area elementary, middle, and high schools, along with universities as well. Federal, state, and local partners are working to identify where the calls are originating from.
Department of Justice
Implementing a Body-Worn Camera Program: Recommendations and Lessons Learned
Police leaders who have deployed body-worn cameras say there are many benefits associated with the devices. They note that body-worn cameras are useful for documenting evidence; officer training; preventing and resolving complaints brought by members of the public; and strengthening police transparency, performance, and accountability. In addition, given that police now operate in a world in which anyone with a cell phone camera can record video footage of a police encounter, body-worn cameras help police departments ensure events are also captured from an officer’s perspective.
Intelligence Fusion Centers, Maryland
(U//FOUO/LES) Maryland Fusion Center Criminal Use of Police Scanner Apps and RadioReference.com
During several recent contacts with criminal gang members, an identified Maryland law enforcement agency has heard their radio transmissions broadcast over a suspect’s smartphone. In one incident, officers pursuing a suspect on foot overheard the suspect listening to the pursuing officers’ radio transmission over a smartphone. The radio broadcasts of the agency’s primary secure law enforcement channel had an approximate delay of three seconds on the suspect’s smartphone. Further investigation revealed that the general public, as well as criminal gang members and associates, are utilizing the website www.radioreference.com to listen to law enforcement secure channels streaming via the Internet. Registration and access to the site is free, with advanced features available to premium subscribers. A customer is able to search radio frequencies throughout the country by state, metro area, city and/or zip code. The website advertises a search for trunked frequencies as well. The frequencies are obtained over the Internet and any cell phone that has web access can listen in.
Belgium, Department of State
(U//FOUO) U.S. State Department Social Media Landscape: Belgium
The social media landscape in Belgium has grown considerably over the last few years and Belgians appear to be increasingly proactive in their social media endeavors as Internet access is obtainable from many electronic sources. All generations, young and old have familiarized themselves with the cell phone, iphone, Blackberry and Netbook usage in order to access social media sites while on the move. The rise in Internet access via mobile devices has created an abundance of new social media users.
Department of Homeland Security, Federal Bureau of Investigation, National Counterterrorism Center
(U//FOUO) DHS-FBI-NCTC Bulletin: Dissemination of Tactics, Techniques, and Procedures Used by Buffalo Attacker Likely To Enhance Capabilities of Future Lone Offenders

This Joint Intelligence Bulletin (JIB) provides an overview of significant tactics, techniques, and procedures (TTPs) discussed or used by the alleged perpetrator of the 14 May 2022 mass casualty shooting in Buffalo, New York and details how related documents spread after the attack may contribute to the current threat landscape. The alleged attacker drew inspiration from previous foreign and domestic racially or ethnically motivated violent extremists (RMVEs) and their online materials, underscoring the transnational nature of this threat. DHS, FBI, and NCTC advise federal, state, local, tribal, and territorial government counterterrorism and law enforcement officials and private sector security partners to remain vigilant of this enduring threat.
Department of Homeland Security
(U//FOUO) DHS Bulletin: Violent Opportunist Tactics Observed During Civil Disturbances 26-31 May

We assess that violent opportunists will continue to exploit ongoing nationwide lawful protests as a pretext to attempt to disrupt law enforcement operations; target law enforcement personnel, assets, and facilities; and damage public and private property. We have identified multiple tactics currently at play, including the use of weapons, counter-mobility, physical barriers, screening and concealment, intercepted communications, and pre-operational activities.
China, Federal Bureau of Investigation
(U//FOUO) FBI Counterintelligence Note: Update on Huawei Chinese Government-Subsidized Telecommunications Company March 2018

With the expanded use of Huawei Technologies Inc. equipment and services in US telecommunications service provider networks, the Chinese Government’s potential access to US business communications is dramatically increasing. China’s intelligence services and Chinese cyber actors could exploit Chinese Government-supported telecommunication equipment on US networks operating as an advanced persistent threat. China makes no secret that its cyber warfare strategy is predicated on controlling global communications network infrastructure.
Florida
Marjory Stoneman Douglas High School Shooting Public Safety Commission Draft Report
On February 14, 2018, fourteen students and three staff members at the Marjory Stoneman Douglas High School in Parkland Florida were fatally shot and seventeen others were wounded, in one of the deadliest school massacres in United States’ history. The gunman Nikolas Cruz, age 19 at the time of the incident, was a former student of Marjory Stoneman Douglas High School. Cruz was a troubled child and young adult who displayed aggressive and violent tendencies as early as 3-years-old. Cruz struggled in academics and attended several schools. There are reports of behavioral issues at all of the schools he attended. He was under the care of mental health professionals from age 11 until he turned age 18 and refused further services. At 2:19 p.m. on February 14, 2018, Cruz exited an Uber ride sharing service at Marjory Stoneman Douglas High School armed with a rifle and several hundred rounds of ammunition concealed in a rifle bag. He entered the school through an unstaffed gate that had been opened for school dismissal and made his way towards building 12 on the North side of campus. He entered the east side of building 12 through an unlocked and unstaffed door. He made his way through all three floors firing into classrooms and hallways and killing or wounding 34 individuals. He exited building 12 and ran across campus, blending in with students evacuating. Cruz was apprehended approximately 1 hour and 16 minutes after the first shots and charged with 17 counts of premeditated murder and 17 counts of attempted murder.
Federal Bureau of Investigation
(U//FOUO) FBI Report: ATM Skimmers Target Standalone ATMs with Wiretap Devices
The purpose of this LIR is to inform DSAC and other relevant private sector partners about new methods ATM skimming crews use to target standalone or kiosk-style ATM terminals such as those found at casinos, hotels, airports, shopping malls, gas stations, restaurants, and supermarkets. The skimming crews intercept customers’ account data through the ATMs’ external cables. The activity observed to date in the United States was discovered at convenience store locations in California, Delaware, and Pennsylvania. This LIR provides details on the methods used in these skimming attempts as well as previously reported use of internal wiretap skimming devices.
Intelligence Fusion Centers, Massachusetts
(U//FOUO) Boston Regional Intelligence Center Suspicious Activity Behavior & Indicators For Public Sector Partners
This document is intended to highlight several suspicious activity behaviors and indicators that may be indicative of preoperational terrorist activity for business owners and private sector security personnel. This product focuses on behaviors and indicators that would be of interest prior to any major event. This proactive public safety strategy is an ongoing attempt to provide our private sector partners with some information on suspicious activity.
Missouri, Panama
(U//FOUO) Missouri National Guard Panama Electronic Surveillance Training Presentations
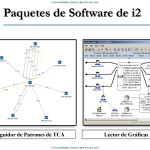
A set of training presentations created by the Missouri National Guard through its State Partnership Program with the the Republic of Panama. The presentations include training on the use of multiple tools for analyzing information obtained through electronic surveillance including Pen-Link and i2 Analyst’s Notebook.
